1,250+ C2 servers mapped across Russian hosting providers in new Hunt.io analysis

A new Hunt.io infrastructure study says more than 1,250 active command-and-control servers were found across 165 Russian infrastructure providers over a 90-day window from January 1 to April 1, 2026. The report frames the finding as a provider-level view of malicious infrastructure rather than a list of isolated IPs, which makes it more useful for defenders trying to spot concentration patterns and repeat abuse across hosting networks.
Hunt.io says C2 infrastructure made up the overwhelming majority of the malicious activity it observed. Across roughly 1,290 malicious artifacts in the dataset, 1,252 were classified as active C2 servers, or about 88.6% of the total. The rest included malicious open directories, phishing sites, and smaller numbers of public IOCs.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
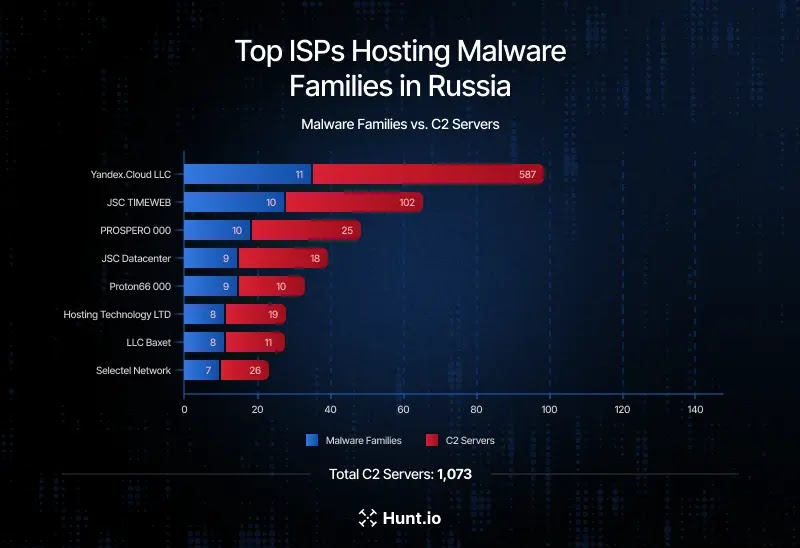
The report also points to concentration among a handful of providers. Hunt.io says TimeWeb led the list with 311 detected C2 servers during the period, followed by WebHost1 with 140, REG.RU with 138, VDSina with 86, and PROSPERO OOO with 80.
What Hunt.io found inside Russian hosting
Hunt.io used its Host Radar system to tie malicious infrastructure back to the providers hosting it. Instead of focusing only on single indicators, the company looked at how infrastructure clusters, reappears, and spreads across shared hosting, VPS environments, and telecom-linked networks.
That approach matters because blocking one IP at a time often fails when threat actors can quickly rotate servers. Provider-level visibility gives defenders a better way to prioritize watchlists, outbound filtering, and infrastructure monitoring around networks that repeatedly host malicious operations. This is an inference based on the provider-focused design described in Hunt.io’s report.
The report does not claim every provider knowingly supports malicious activity. It shows that these networks hosted large amounts of it during the observation period. That distinction matters, because commercial hosting environments can contain both normal customer workloads and threat infrastructure at the same time.
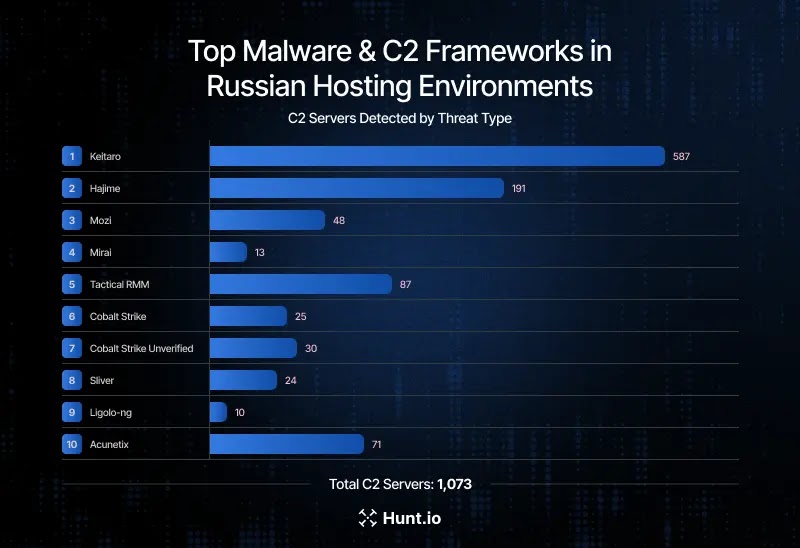
Keitaro, Hajime, and Mirai stood out most
Hunt.io says Keitaro accounted for the largest concentration of identified C2 infrastructure, with 587 unique C2 IP addresses in the dataset. Keitaro is often described as a traffic distribution system, and defenders frequently see it abused to route victims toward malware or scam content.
The next largest families included Hajime with 191 C2 servers, along with Mozi and Mirai, which point to continued abuse of routers, IoT devices, and other edge systems. Hunt.io also found offensive frameworks and dual-use tooling such as Tactical RMM, Cobalt Strike variants, Sliver, Ligolo-ng, Acunetix, Interactsh, and Gophish.
That mix suggests the infrastructure supports more than one kind of operation. The observed servers appear tied not just to direct malware command-and-control, but also to reconnaissance, credential theft, phishing, red-team-style post-exploitation tooling, and traffic redirection. This conclusion follows from the malware and tool families Hunt.io listed in the report.
Campaign examples linked to the infrastructure
Hunt.io tied several active campaigns to the hosting environment it analyzed. One example involved a ClickFix-style lure on JSC TIMEWEB that pushed users to run a PowerShell command which then delivered Latrodectus v2.3 and connected to attacker-controlled domains.
The report also linked REG.RU-hosted infrastructure to a Lumma Stealer campaign that used Google Groups redirectors to deliver malicious archives across Windows and Linux systems. On Hosting Technology LTD infrastructure, Hunt.io connected the SmartApeSG campaign to Remcos RAT delivery through fake CAPTCHA prompts and DLL sideloading persistence.
Another case involved Beget LLC infrastructure and the UAC-0252 campaign, which impersonated Ukrainian government institutions and deployed SHADOWSNIFF and SALATSTEALER by abusing a WinRAR flaw tracked as CVE-2025-8088. Hunt.io also linked Proton66 OOO infrastructure to a BoryptGrab infostealer campaign that abused more than 100 public GitHub repositories through SEO poisoning.
Russian hosting exposure at a glance
| Metric | Hunt.io finding |
|---|---|
| Observation window | January 1 to April 1, 2026 |
| Russian providers observed with malicious infrastructure | 165 |
| Total malicious artifacts | About 1,290 |
| Confirmed C2 servers | 1,252 |
| C2 share of total artifacts | About 88.6% |
| Top provider by detected C2 count | TimeWeb, with 311 |
All figures in the table come from Hunt.io’s published analysis and supporting company posts.
What defenders should take from this
The biggest takeaway is not just that Russian infrastructure hosted many malicious servers. It is that the same provider environments repeatedly surfaced across commodity crime, malware delivery, phishing, and post-exploitation tooling. That makes provider-level monitoring more valuable than relying only on file hashes or short-lived single IP indicators. This is an inference from the structure and findings of the Hunt.io report.
Security teams should also pay attention to outbound traffic. Hunt.io’s findings support tighter scrutiny of connections to Russian ASNs and providers that show repeated C2 density, especially when systems have no business reason to talk to those networks.
The IoT angle matters too. The presence of Hajime, Mozi, and Mirai infrastructure shows that routers, cameras, and edge devices still feed the broader threat ecosystem. Defenders who ignore those assets may miss part of the infection chain or the attacker’s fallback infrastructure.
What security teams should do now
- Monitor outbound connections to high-risk providers and ASNs that repeatedly appear in malicious infrastructure reporting.
- Expand threat intelligence beyond malware hashes to include hosting-provider patterns, redirectors, and infrastructure clusters.
- Watch for ClickFix-style PowerShell chains, especially where users copy and run commands from fake CAPTCHA pages.
- Keep visibility on routers, cameras, and other edge devices that can feed botnet infrastructure tied to Hajime, Mozi, or Mirai.
- Treat repeated connections to providers such as TimeWeb, REG.RU, WebHost1, VDSina, and PROSPERO OOO as signals worth deeper investigation, not automatic proof of compromise.
FAQ
Hunt.io says it identified 1,252 active C2 servers across 165 Russian infrastructure providers over a three-month period ending April 1, 2026.
TimeWeb had the highest reported count in the study, with 311 detected C2 servers over 90 days.
No. The report shows that malicious infrastructure was present inside those provider environments. It does not, by itself, prove provider intent or cooperation. That distinction follows from the way Hunt.io describes the findings.
Because provider-level infrastructure analysis helps teams spot repeat abuse patterns, prioritize monitoring, and catch malicious traffic that might not stand out when viewed as one IP or one domain at a time. This is a reasoned conclusion based on the methodology Hunt.io describes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages