MiningDropper is pushing Android infostealers, RATs, and banking malware through fake apps, Cyble says

A fast-growing Android malware campaign is using a framework called MiningDropper to deliver far more dangerous payloads through fake mobile apps, according to Cyble. The researchers describe it as a modular dropper that can install infostealers, banking malware, remote access trojans, and even cryptocurrency miners after the victim downloads a trojanized APK.
Cyble says the campaign spreads through phishing pages, social media links, and fraudulent websites that impersonate transport services, banks, telecom brands, and popular apps. The real danger is not just the fake app itself, but the layered delivery system behind it, which lets attackers swap the final payload depending on the target or campaign.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The company says it observed more than 1,500 MiningDropper samples in the wild over the past month, with clusters targeting users in India as well as victims across Europe, Latin America, and Asia. That suggests MiningDropper is no longer a niche Android threat. It is becoming a reusable malware framework that multiple campaigns can deploy at scale.
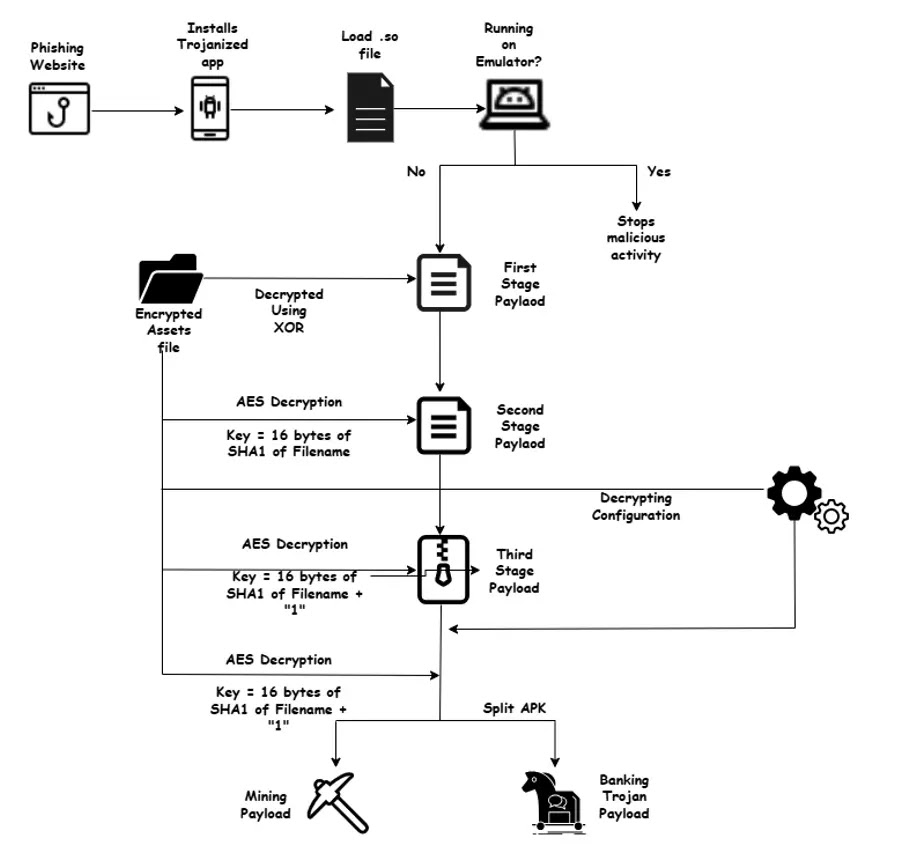
How the Android infection chain works
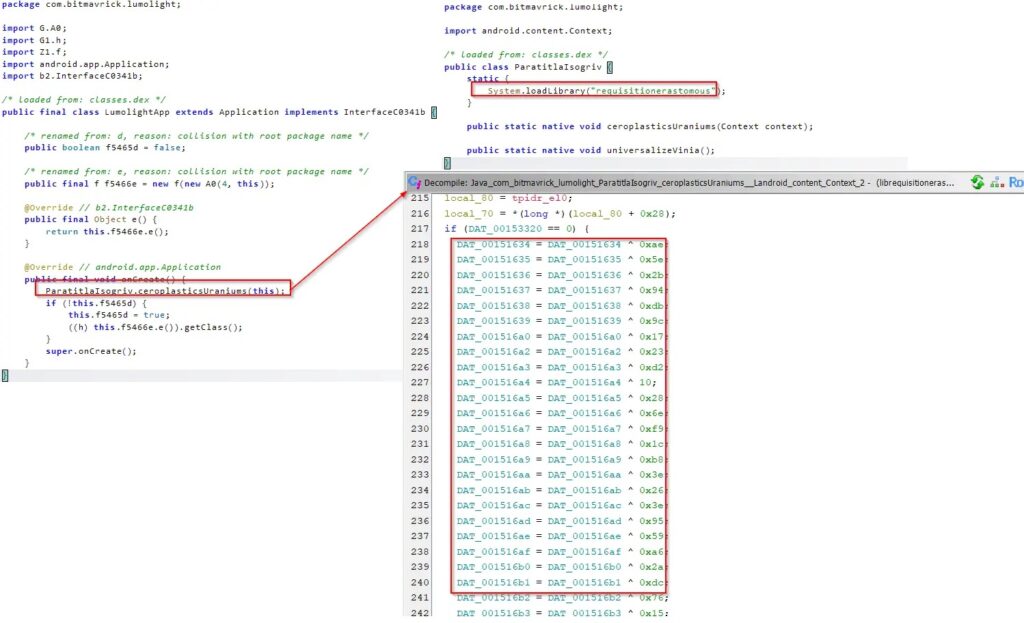
Cyble says the chain starts with a trojanized build of the open-source Android project LumoLight. From there, malicious actions begin inside a native library called librequisitionerastomous.so, where strings stay hidden with XOR obfuscation and only decrypt at runtime. That design makes the sample harder to inspect and helps it stay below simple static detection thresholds.
The malware also checks device architecture, platform details, and model information before it continues. Cyble says these anti-emulation and anti-analysis checks let the malware stop early if it believes it is running inside a sandbox, emulator, or researcher-controlled environment. That helps explain why some samples show low detection despite broad distribution.
If those checks pass, the native code decrypts a first-stage payload and loads it with DexClassLoader, then decrypts a second-stage file with AES. Cyble says the next stage can show a fake Google Play update screen while it pulls configuration data and decides whether to activate a mining path or a user-defined malware payload path for later installation.
Why MiningDropper stands out
What makes this campaign more serious than an ordinary fake APK scam is its flexibility. Cyble says MiningDropper is not tied to one final malware family. It acts as a delivery framework, which means threat actors can use the same infrastructure and infection logic to push different payloads without rebuilding the entire operation each time.
One of the payloads linked to this ecosystem is BTMOB RAT. Cyble described BTMOB earlier as an Android threat that abuses Accessibility Services, supports remote control, steals credentials, captures screens, records audio, and exfiltrates sensitive data. Those capabilities fit neatly into the MiningDropper model, where the dropper handles delivery and the final payload handles theft, surveillance, or fraud.
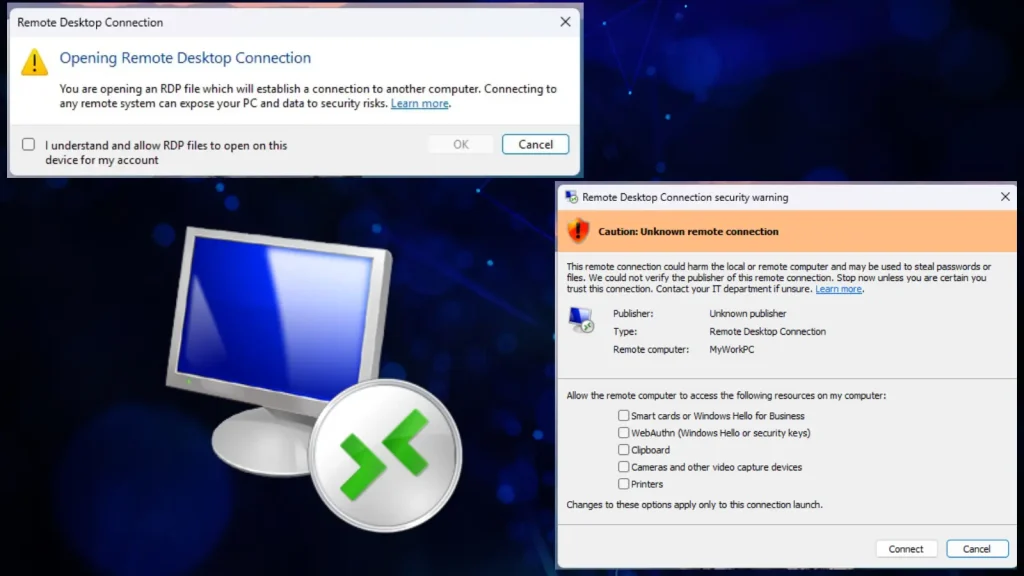
The campaign also reflects a bigger Android security problem. Google says recent analysis found more than 90 times more malware from sideloaded sources than from Google Play. That does not mean Google Play is perfect, but it does show why phishing pages and fake download sites remain such effective malware channels on Android.
What users should do now
The most important defense is to avoid installing APKs from links in messages, social posts, or cloned websites. Google’s Play Protect guidance says Android checks apps during installation and can scan apps from outside Google Play, but users still need to avoid risky installs in the first place because sideloading remains a major source of malware exposure.
Users should also check app permissions carefully, especially if an app asks for Accessibility access, screen visibility, notification access, or broad device control without a clear reason. In campaigns like this one, those permissions often enable credential theft, remote control, overlay abuse, or financial fraud after the dropper finishes installing the next stage. This is an inference based on the payload capabilities Cyble documented, not a separate Google statement.
For organizations, the lesson is broader than one malware name. MiningDropper shows how Android threats now separate delivery, deception, and monetization into reusable layers. That lets attackers pivot quickly between banking theft, credential harvesting, remote access, and silent crypto mining while keeping the front-end lure almost the same.
MiningDropper at a glance
| Area | What Cyble says |
|---|---|
| Main distribution | Phishing pages, social links, and fake branded websites delivering malicious APKs. |
| Framework type | Modular Android dropper used to install different final payloads. |
| Technical evasion | Native code, XOR obfuscation, encrypted assets, dynamic DEX loading, and anti-emulation checks. |
| Notable payloads | Infostealers, BTMOB RAT, banking malware, and crypto miners. |
| Geographic reach | India, Europe, Latin America, and Asia. |
| Sample volume | More than 1,500 observed in the past month. |
Key steps to reduce risk
- Install apps only from trusted stores and avoid direct APK downloads from links.
- Keep Google Play Protect enabled and pay attention to warnings about harmful apps or unsafe URLs.
- Treat fake update prompts and branded download pages with caution, especially outside official app stores.
- Review Accessibility and high-risk permissions before approving them.
- Use MFA for banking and other sensitive accounts so a stolen password alone does less damage. This is a standard defensive recommendation inferred from the infostealer and banking malware risk described by Cyble.
FAQ
Cyble describes it as a modular Android malware framework that delivers other threats, including infostealers, banking malware, RATs, and miners, through staged payloads hidden inside fake apps.
Because the malware uses native code, encrypted assets, dynamic loading, and anti-emulation checks. Those layers hide the final payload until later in the infection chain.
Yes, based on the public reporting. Cyble says victims land on phishing or fake download sites, and Google says sideloaded sources carry far more malware risk than Google Play.
Cyble linked MiningDropper activity to BTMOB RAT, which supports remote control, credential theft, screen capture, audio recording, and data theft on Android devices.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages