New ClickFix Attack Uses Cmdkey and Regsvr32 Instead of PowerShell to Evade Detection

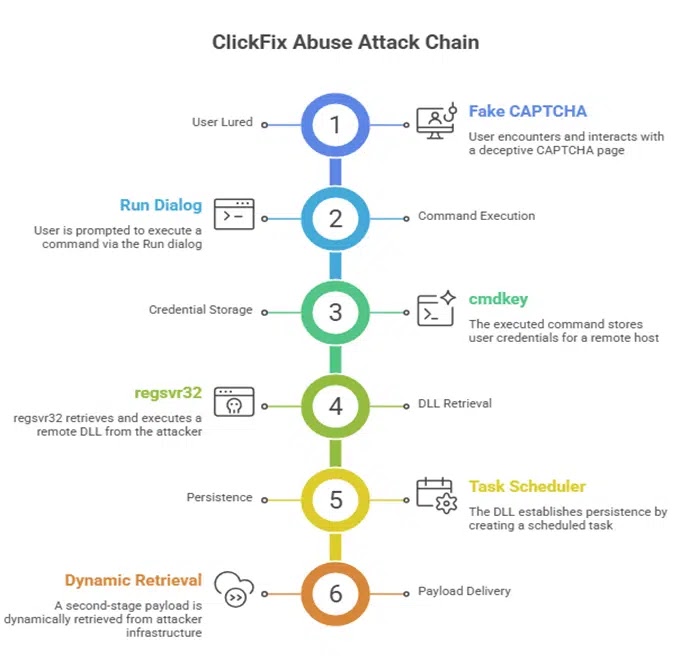
A new ClickFix variant is replacing PowerShell with native Windows tools, making the social engineering attack harder for security teams to detect. The campaign tricks users into running a command through the Windows Run dialog, then uses cmdkey and regsvr32 to load a remote DLL from attacker-controlled infrastructure.
ClickFix attacks rely on user deception rather than a software exploit. Victims usually land on a fake CAPTCHA or verification page that tells them to press Win + R, paste a command, and press Enter. Microsoft has warned that this extra user action can help ClickFix campaigns slip past conventional and automated defenses.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This version matters because it avoids PowerShell, which many endpoint tools monitor closely. Instead, it chains built-in Windows utilities, also known as living-off-the-land binaries, to store credentials, load a remote DLL, and create persistence with fewer obvious files left on disk.
How the new ClickFix attack works
CyberProof’s Threat Research Team reported the new variant on April 22, 2026. The researchers found that attackers use a fake CAPTCHA-style page to convince victims to run a prebuilt command through the Windows Run dialog.
The command first uses cmdkey to store credentials for the remote IP address 151.245.195[.]142 under the username guest. It then uses regsvr32 to silently load demo.dll from a remote SMB share through a UNC path.
The command also includes a REM comment that reads “I am not a robot.” This makes the pasted command look connected to the fake verification step and helps hide the real purpose from less technical users.
Key details of the campaign
| Item | Details |
|---|---|
| Technique | ClickFix social engineering |
| Initial lure | Fake CAPTCHA or verification page |
| User action | Press Win + R, paste command, press Enter |
| Main Windows tools abused | cmdkey, regsvr32, cmd.exe, Task Scheduler |
| Payload delivery | Remote DLL loaded from SMB share |
| Persistence method | Scheduled task |
| Scheduled task name | RunNotepadNow |
| Remote IP | 151.245.195[.]142 |
| Reported DLL path | \\151.245.195.142\hi\demo.dll |
| Reported XML path | \\151.245.195.142\hi\777.xml |
Why replacing PowerShell changes the risk
Many security teams already watch PowerShell for suspicious download cradles, encoded commands, and script execution. That has pushed attackers to test other built-in Windows tools that may receive less attention.
In this campaign, regsvr32 loads and executes the remote DLL. When the DLL runs, its DllRegisterServer export launches a hidden CreateProcessA call that creates a scheduled task through schtasks.
CyberProof said the task definition does not sit locally on the infected machine. Instead, the system pulls it from a remote XML file hosted on the attacker’s SMB infrastructure. This lets attackers update the second-stage payload without changing the first-stage DLL.
Why this is hard to detect
The attack uses normal Windows components, which makes it difficult to separate malicious activity from legitimate administration. cmdkey can store credentials, regsvr32 can register DLLs, and Task Scheduler can automate routine jobs.
That normal behavior creates the detection challenge. Security tools that focus only on dropped malware files may miss an attack chain that uses remote payloads and trusted binaries.
The campaign also reflects a wider ClickFix trend. Recent reports show attackers moving beyond classic PowerShell commands and testing variants that use WebDAV, rundll32, remote shares, and other native execution paths.
Indicators of compromise
| Type | Indicator |
|---|---|
| IP address | 151[.]245[.]195[.]142 |
| Remote DLL | \\151[.]245[.]195[.]142\hi\demo.dll |
| Remote XML | \\151[.]245[.]195[.]142\hi\777.xml |
| SHA-256 | b2d9a99de44a7cd8faf396d0482268369d14a315edaf18a36fa273ffd5500108 |
| Scheduled task | RunNotepadNow |
Security teams should treat these indicators as starting points, not complete coverage. Attackers can change infrastructure, DLL names, share paths, and task names quickly.
How organizations can defend against this ClickFix variant
Organizations should monitor cmdkey activity that involves external IP addresses. In normal environments, users rarely need to store credentials for unknown public IPs through cmdkey.
Teams should also alert when regsvr32 loads DLLs from remote UNC paths. This behavior deserves close review because attackers commonly abuse regsvr32 for proxy execution and defense evasion.
Recommended actions:
- Monitor
cmdkeycommands that reference external IP addresses. - Alert on
regsvr32loading DLLs from UNC paths. - Block outbound SMB traffic to the internet.
- Review scheduled tasks created through
schtasks. - Flag scheduled tasks that reference remote XML files.
- Monitor command chains launched through
cmd.exe. - Review Run dialog execution history through RunMRU artifacts.
- Train users never to paste commands from CAPTCHA pages.
- Add fake CAPTCHA and ClickFix examples to security awareness training.
- Restrict LOLBin abuse through endpoint detection rules and application control.
What users should watch for
A legitimate CAPTCHA should never ask users to open the Windows Run dialog, paste a command, or run system tools.
Any page that asks for Win + R, Ctrl + V, or command execution should be treated as malicious. Users should close the page and report it to their security team.
This simple rule can stop most ClickFix attacks before the command runs.
FAQ
ClickFix is a social engineering technique that tricks users into running malicious commands themselves, often through fake CAPTCHA or browser verification pages.
This variant avoids PowerShell and uses cmdkey with regsvr32 to load a remote DLL from attacker-controlled infrastructure.
Security tools often monitor PowerShell closely. By switching to other built-in Windows tools, attackers may reduce detection visibility.
The initial delivery relies on remote DLL loading through a UNC path. CyberProof reported that the campaign avoids dropping an initial executable to disk.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages