China-linked hackers target Asian governments, NATO state, journalists, and activists

China-aligned hackers have targeted government and defense organizations across Asia, while separate China-linked phishing campaigns have gone after journalists, activists, and diaspora communities, according to new security research.
Trend Micro is tracking one of the espionage campaigns as SHADOW-EARTH-053. The group has targeted organizations in South, East, and Southeast Asia, along with one NATO government in Europe.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Citizen Lab also reported two China-aligned phishing clusters, GLITTER CARP and SEQUIN CARP, aimed at journalists and civil society groups, including Uyghur, Tibetan, Taiwanese, and Hong Kong diaspora activists.
What researchers found
Trend Micro said SHADOW-EARTH-053 has been active since at least December 2024. The group focuses on government, defense, transportation, technology, and critical infrastructure targets.
The campaign relies heavily on old but still useful vulnerabilities in internet-facing Microsoft Exchange and IIS servers. In many cases, attackers exploit systems that should already have received security updates.
After gaining access, the attackers deploy web shells, move through the network, and install ShadowPad malware through DLL sideloading. ShadowPad has long been associated with China-linked espionage operations.
At a glance
| Campaign or cluster | Main targets | Main tactics | Reported by |
|---|---|---|---|
| SHADOW-EARTH-053 | Government, defense, transportation, technology, and critical infrastructure | Exchange and IIS exploitation, web shells, ShadowPad, DLL sideloading | Trend Micro |
| GLITTER CARP | ICIJ members, journalists, activists, and diaspora communities | Credential phishing, impersonation, fake login pages, tracking pixels | Citizen Lab |
| SEQUIN CARP | Journalists covering China-linked repression and ICIJ-related topics | Social engineering, fake personas, OAuth abuse, account access attempts | Citizen Lab |
Countries and regions targeted
Trend Micro’s research points to victims in Pakistan, Thailand, Malaysia, India, Myanmar, Sri Lanka, Taiwan, and Poland. The inclusion of Poland shows that the campaign extends beyond Asia into a NATO member state.
The researchers also found overlap with another tracked cluster called SHADOW-EARTH-054. Nearly half of the observed targets had signs of earlier compromise by that related activity set.
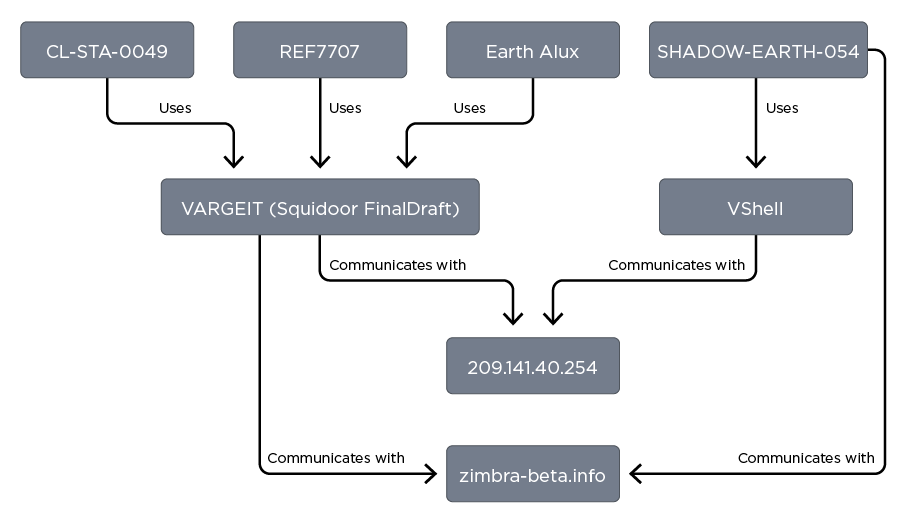
Trend Micro said the overlap does not prove direct coordination. It may show that multiple China-aligned groups are exploiting the same exposed systems and reusing similar tools.
How SHADOW-EARTH-053 breaks into networks
The group’s first step usually involves internet-facing servers. Trend Micro highlighted Microsoft Exchange and IIS applications as major entry points.
One important example is the ProxyLogon chain, a group of Microsoft Exchange vulnerabilities disclosed in 2021. Years later, these flaws still help attackers compromise organizations that have not patched legacy systems.
Once inside, the hackers deploy Godzilla web shells for command execution and persistence. They then stage ShadowPad implants through DLL sideloading with legitimate signed executables.
Tools seen in the campaign
- Godzilla web shells for persistent access and command execution
- ShadowPad malware for espionage and long-term control
- AnyDesk for remote access in some parts of the intrusion chain
- IOX, GOST, and Wstunnel for tunneling and covert communication
- RingQ for packing malicious binaries and avoiding detection
- Mimikatz for credential access and privilege escalation
- Sharp-SMBExec and custom RDP launchers for lateral movement
- Noodle RAT on Linux systems in at least one React2Shell-related case
React2Shell also appears in the wider activity
Trend Micro said at least one case involved exploitation of React2Shell, tracked as CVE-2025-55182. The flaw affected React Server Components and drew rapid exploitation attempts after disclosure in late 2025.
In that case, the attack led to deployment of a Linux version of Noodle RAT. Google Threat Intelligence Group linked that chain to a group tracked as UNC6595.
The React2Shell example shows how quickly major web application flaws can become part of espionage operations. Once public exploit details spread, state-linked groups often test and adapt them against live targets.
Journalists and activists face separate phishing campaigns
Citizen Lab’s research focused on two China-aligned actors that targeted and impersonated journalists and civil society members. The research was conducted with the International Consortium of Investigative Journalists.
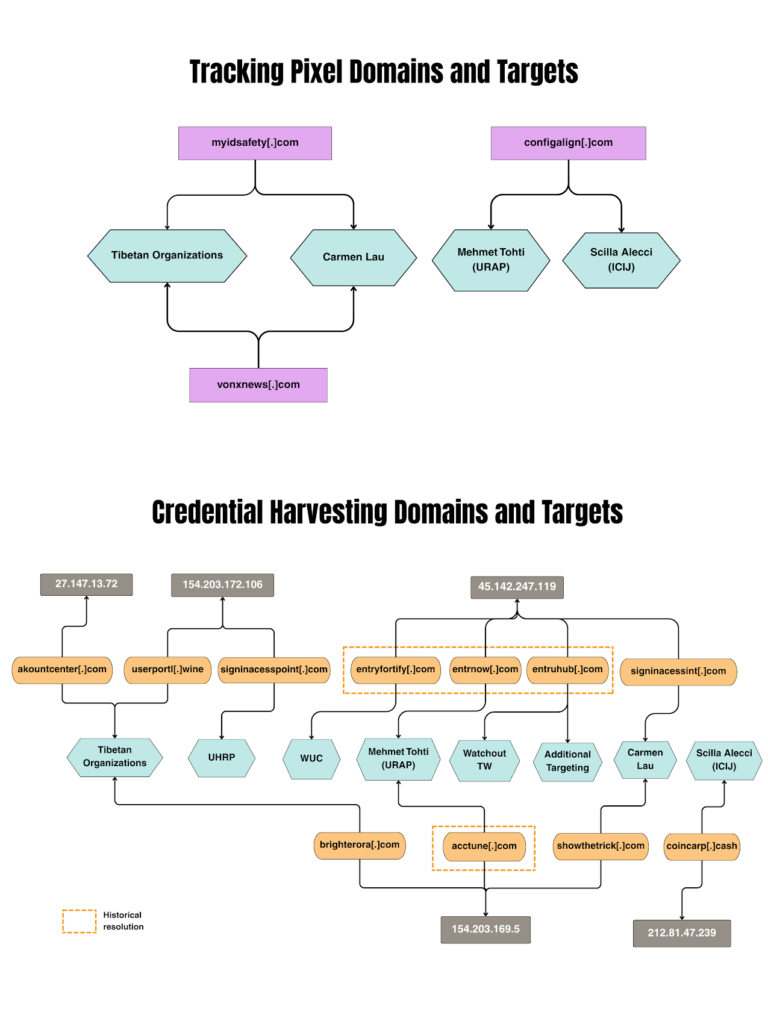
GLITTER CARP has run broad phishing and impersonation campaigns since April 2025. Targets included Uyghur, Tibetan, Taiwanese, and Hong Kong diaspora activists, along with journalists reporting on those communities.
SEQUIN CARP has focused more heavily on journalists, including ICIJ journalist Scilla Alecci and other reporters covering issues that matter to the Chinese government.
How the phishing attacks worked
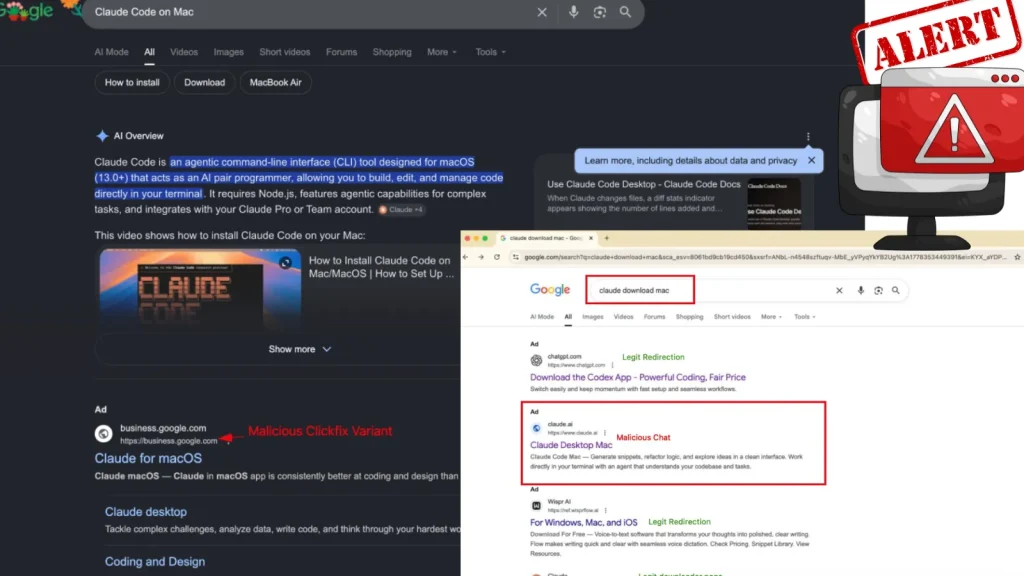
The attackers used detailed impersonation schemes instead of generic phishing emails. Some messages pretended to come from known individuals, while others impersonated technology company security alerts.
In many cases, victims were sent links to fake Google login pages. These pages were designed to capture email credentials and give attackers access to private communications.
Citizen Lab also found OAuth-based abuse. In that approach, the attacker tries to trick the victim into granting access to a third-party token, which can create persistent account access without needing the password again.
Why this matters
The two sets of activity point to the same broader problem: attackers are combining server exploitation with identity-focused phishing to support intelligence collection.
Government and defense targets face direct network compromise through vulnerable servers. Journalists, activists, and diaspora groups face account takeover attempts through impersonation, fake login pages, and social engineering.
The campaigns also show the value of old vulnerabilities to advanced actors. Even when a flaw has been public for years, attackers can still use it if organizations keep exposed systems unpatched.
What organizations should do now
- Patch Microsoft Exchange and IIS servers with the latest security updates.
- Remove or isolate legacy internet-facing servers that cannot be patched quickly.
- Use IPS or WAF rules to block known exploit attempts when immediate patching is not possible.
- Search for Godzilla web shells and suspicious files on Exchange and IIS servers.
- Monitor for ShadowPad, Noodle RAT, Mimikatz, tunneling tools, and unusual AnyDesk activity.
- Review outbound traffic for IOX, GOST, Wstunnel, and other tunneling behavior.
- Enable phishing-resistant multi-factor authentication for email and cloud accounts.
- Review OAuth app grants and remove suspicious third-party access.
- Train journalists, researchers, and civil society staff to verify unusual document, interview, and security-alert requests.
What this means for defenders
Security teams should treat internet-facing servers and email accounts as connected parts of the same attack surface. A compromised server can give attackers a foothold, while a stolen inbox can expose sources, plans, contacts, and internal documents.
For government and defense organizations, the priority is patching, exposure reduction, and hunting for persistence. For journalists and civil society groups, the priority is account protection, OAuth review, and safer verification habits.
The campaigns also show why digital repression is no longer limited by borders. Attackers can target public institutions, private contractors, reporters, and diaspora communities at the same time, using different tools for the same intelligence goals.
FAQ
SHADOW-EARTH-053 is a temporary name used by Trend Micro for a China-aligned cyberespionage cluster targeting government, defense, and critical infrastructure organizations.
Trend Micro reported targeting in Pakistan, Thailand, Malaysia, India, Myanmar, Sri Lanka, Taiwan, and Poland.
The campaign used Godzilla web shells, ShadowPad, tunneling tools, Mimikatz, Sharp-SMBExec, and other tools for persistence, command execution, credential access, and lateral movement.
GLITTER CARP and SEQUIN CARP are China-aligned phishing clusters identified by Citizen Lab. They targeted journalists, ICIJ members, activists, and diaspora communities.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages