Fake DeepSeek TUI GitHub Repositories Push Rust Malware at Developers

Fake GitHub repositories impersonating DeepSeek TUI are being used to deliver malware to developers and AI users. The campaign abuses interest in AI coding tools by making malicious repositories look like legitimate open-source software pages.
DeepSeek TUI is a real terminal coding agent for DeepSeek models. It runs from the command line, can interact with local workspaces, and is available through the official Hmbown GitHub repository.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
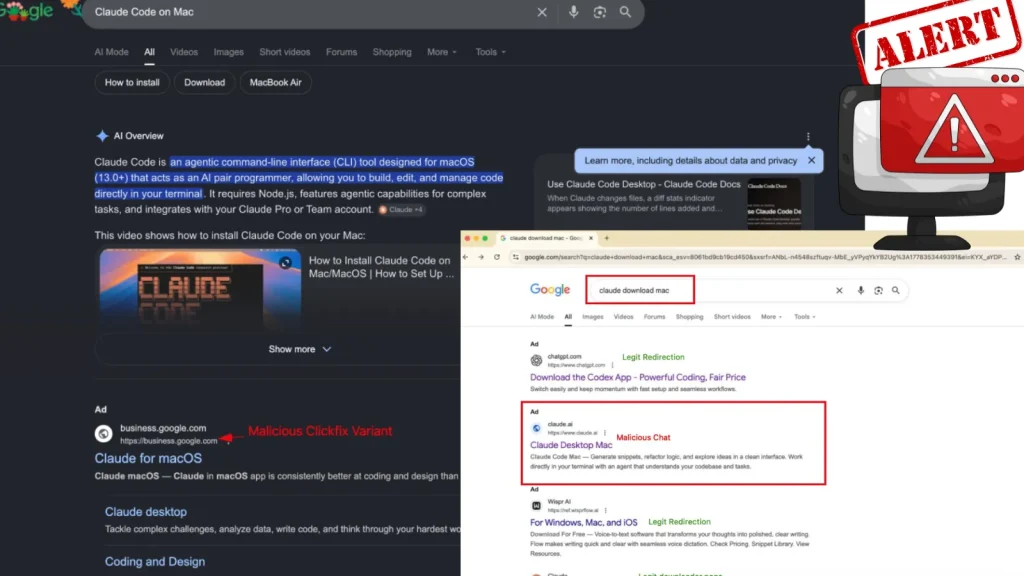
The malicious repositories are separate from the legitimate project. Attackers are using fake release pages and AI-themed file names to trick users into downloading a Rust-based malware family linked to the earlier OpenClaw campaign.
Fake repositories use DeepSeek TUI as the lure
The attack takes advantage of the way developers often download tools from GitHub Releases. A fake repository can look convincing at first glance, especially if it copies a real project’s name, layout, description, and release format.
In this campaign, the malware was hidden inside a compressed archive on a fraudulent GitHub Releases page. The main file identified in the campaign was named DeepSeek-TUI_x64.exe.
Researchers said the same infrastructure also used installers named after other AI tools and services, including Claude, Grok, WormGPT, KawaiiGPT, fraudGPT, and Kimi-themed tools. That suggests the attackers are rotating through trending AI names instead of targeting only one project.
Key facts at a glance
| Item | Details |
|---|---|
| Main lure | Fake DeepSeek TUI GitHub repositories |
| Target audience | Developers, AI users, and open-source tool users |
| Main malware file | DeepSeek-TUI_x64.exe |
| Malware language | Rust |
| Linked campaign | OpenClaw-style spoofing activity |
| Main behavior | Anti-sandbox checks, Defender tampering, second-stage downloads, persistence |
| Reported C2 domains | mikolirentryifosttry.info and zkevopenanu.cfd |
How the malware avoids early detection
Before the malware performs its main actions, it checks whether it is running inside a virtual machine, sandbox, or analysis environment. This helps it avoid researchers and automated malware scanners.
If the environment looks suspicious, the malware shows a fake error message saying the system does not meet the minimum requirements. Then it exits without revealing the full infection chain.
If the machine looks like a real user system, the malware continues execution. It then uses an XOR-encrypted PowerShell script to weaken Windows Defender protections.
Windows Defender settings are changed
The malware adds multiple folder exclusions to Windows Defender. It also disables cloud-based reporting and behavior monitoring, which can reduce the chance of early detection.
It also opens inbound firewall ports 57001, 57002, and 56001. These changes can give the attacker more room to stage payloads, communicate with infected systems, or prepare later actions.
The reported string decryption key used in the sample is xnasff3wcedj. The malware also contacts Pastebin and snippet.host links to fetch additional payloads hosted through Azure.
Second-stage payloads help maintain access
The campaign uses several second-stage components, and each one handles a different part of the infection. OneSync.exe and WinHealhCare.exe support installation and scheduled task setup while reporting activity through Telegram.
The file onedrive_sync.exe helps the malware persist through the Windows Run registry key. Another component, svc_service.exe, acts as the resident core and uses NT syscalls for thread injection.
The loader autodate.exe pretends to be a service manager while injecting payloads into memory. This in-memory approach can make the malware harder for file-based scanners to catch.
Why developers face higher risk
Developer machines are valuable targets because they often hold SSH keys, API tokens, GitHub credentials, cloud access, and source code. A fake AI tool can give attackers a direct path into those environments.
The campaign also shows how attackers now follow developer trends closely. When a new AI tool gains attention, criminals can quickly create lookalike repositories and release pages to capture search traffic.
This creates a simple but serious risk. Users may trust a GitHub page because it looks technical and familiar, even when the repository has no real history, no genuine contributors, and no trusted release process.
How to check a GitHub repository before downloading
- Check whether the repository belongs to the real maintainer or organization.
- Review the account creation date and contribution history.
- Look at commit history before trusting a release file.
- Check whether issues, pull requests, and releases look natural.
- Avoid repositories that appeared suddenly around a trending tool name.
- Do not run compressed executable files from unknown GitHub Releases pages.
- Use official package managers or official repositories whenever possible.
What security teams should monitor
Security teams should review systems that recently downloaded DeepSeek-themed or AI-themed executables from GitHub. They should especially watch for the file DeepSeek-TUI_x64.exe and related fake installers.
Teams should also monitor for unusual PowerShell activity that changes Microsoft Defender settings. Commands that add Defender exclusions or disable cloud protection deserve urgent review.
Network teams should check for traffic to the reported C2 domains mikolirentryifosttry.info and zkevopenanu.cfd. They should also review access to suspicious Pastebin and snippet.host payload staging links tied to this campaign.
FAQ
No. The reported campaign uses fake GitHub repositories that impersonate DeepSeek TUI. The legitimate project is hosted under the Hmbown GitHub account.
The main first-stage file reported in the campaign is DeepSeek-TUI_x64.exe. Researchers also listed many other AI-themed fake installer names tied to the same infrastructure.
AI tools attract developers and early adopters. Attackers use trending AI names to make fake repositories look timely, useful, and believable.
The malware checks for sandboxes, weakens Windows Defender settings, downloads second-stage payloads, and sets up persistence through scheduled tasks, registry keys, Winlogon hooks, and startup shortcuts.
Summary
- Attackers are using fake DeepSeek TUI GitHub repositories to spread malware.
- The malicious files are separate from the legitimate DeepSeek TUI project.
- The campaign uses Rust malware linked to OpenClaw-style spoofing activity.
- The malware can weaken Windows Defender and install persistent second-stage payloads.
- Developers should verify GitHub repositories carefully before downloading AI tools.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages