Fake Claude Website Spreads New Beagle Backdoor Through Windows Installer

A fake Claude website is being used to spread a newly documented Windows backdoor named Beagle. Security researchers say the campaign impersonates Anthropic’s Claude AI assistant and pushes a malicious Windows installer through a domain designed to look related to the real service.
The fake site offered a download called Claude-Pro Relay through a large ZIP archive. Once opened, the installer placed malicious files in the Windows Startup folder so the malware could run again after every reboot.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Sophos X-Ops said the attack chain looked similar to older PlugX-style campaigns because it used DLL sideloading, a signed legitimate executable, and an encrypted payload file. However, the final payload was not PlugX. It was a previously undocumented backdoor that Sophos named Beagle.
Fake Claude site used AI interest as the lure
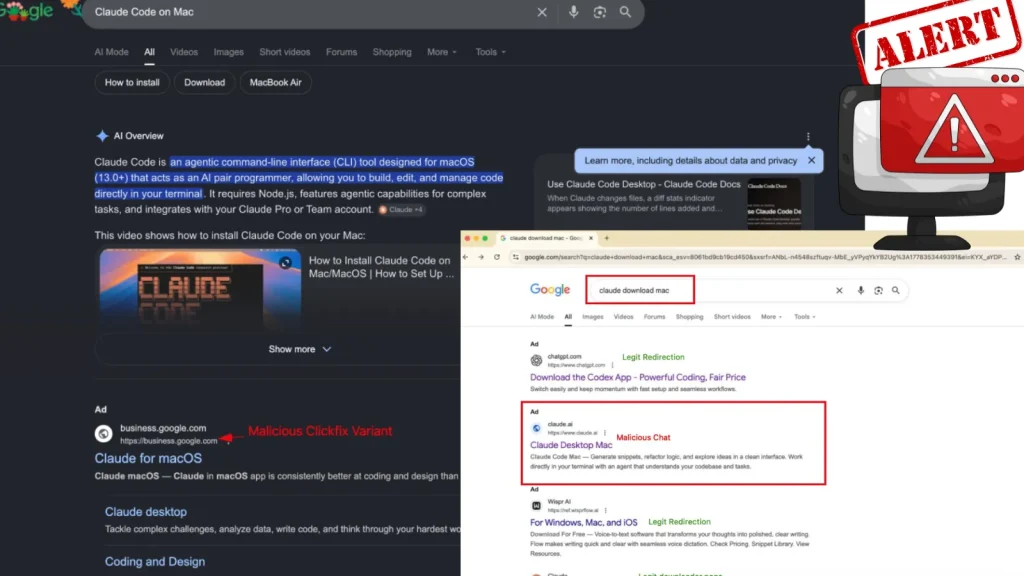
The malicious domain, claude-pro[.]com, copied parts of the real Claude design, including similar colors and fonts. Sophos said the fake page looked much simpler than the legitimate site, and many links redirected back to the same front page.
The site appeared to target people searching for Claude-related desktop tools, especially developers interested in Claude Code. The fake product name, Claude-Pro Relay, was presented as a high-performance relay service.
Researchers believe the campaign may have used malvertising, where attackers pay to place harmful links in search ads or sponsored results. SEO poisoning may also have helped the fake site appear in searches for Claude downloads.
Key details at a glance
| Item | Details |
|---|---|
| Fake domain | claude-pro[.]com |
| Malicious download | Claude-Pro-windows-x64.zip |
| Installer inside archive | Claude.msi |
| Malware chain | DLL sideloading, DonutLoader, Beagle backdoor |
| Persistence method | Files placed in the Windows Startup folder |
| Main risk | Remote command execution, file transfer, and persistent access |
| Safe download source | Official Claude download page |
How the malware gets installed
The infection starts when a user downloads the ZIP archive and runs the Claude.msi installer. The installer drops three files into the Windows Startup folder: NOVupdate.exe, NOVupdate.exe.dat, and avk.dll.
NOVupdate.exe is a legitimate signed updater associated with G DATA antivirus products. The attackers abuse that trust by placing a malicious avk.dll file in the same folder, causing the trusted executable to load the attacker-controlled DLL.
This technique is called DLL sideloading. It helps malware hide behind a legitimate signed program, which can make detection harder for some security tools.
DonutLoader delivers the Beagle backdoor
After the malicious DLL runs, it decrypts the payload hidden inside NOVupdate.exe.dat. Sophos said the decrypted content is DonutLoader shellcode, an open-source in-memory loader.
DonutLoader then launches the final malware payload. Sophos identified that payload as Beagle, a backdoor that can receive commands from a remote server.
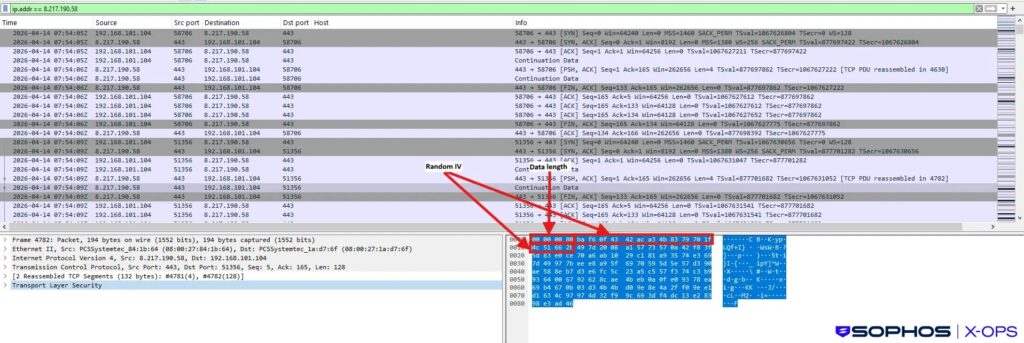
Beagle connects to license[.]claude-pro[.]com over TCP port 443 and UDP port 8080. Sophos said the malware uses a hardcoded AES key to encrypt command-and-control traffic.
What attackers can do after infection
Once Beagle runs on a Windows system, attackers can use it to control parts of the infected machine remotely. The backdoor includes commands for file transfer, directory management, command execution, and self-removal.
That gives attackers a path to maintain access, inspect files, move data, or prepare the system for additional payloads. The campaign does not appear limited to simple adware or nuisance malware.
Related samples found on VirusTotal suggest the operators may have tested or reused parts of the same infrastructure across several months. Sophos found samples from February, March, and April 2026 that shared parts of the same broader pattern.
Why the PlugX comparison matters
PlugX is a long-running remote access Trojan often associated with espionage campaigns. The fake Claude campaign caught attention because its sideloading structure looked similar to PlugX delivery chains.
That comparison does not prove the same operators were involved. Sophos said the campaign may reflect retooling, imitation, or shared techniques rather than a clean attribution link.
The more important point is that attackers are borrowing methods usually seen in more advanced campaigns. They are now applying them to lures based on popular AI tools, where users may be less cautious because they expect to download new software.
How users can stay safe
- Download Claude only from the official Claude website or official app stores.
- Avoid clicking sponsored search ads for software downloads.
- Check the URL carefully before downloading any Claude installer.
- Be cautious with ZIP archives that claim to contain AI desktop tools.
- Look for unusual files in the Windows Startup folder.
- Monitor for connections to claude-pro[.]com and license[.]claude-pro[.]com.
Signs of possible infection
Users who visited the fake site or installed the fake Claude-Pro Relay package should check for suspicious startup files. The main filenames reported in this campaign are NOVupdate.exe, NOVupdate.exe.dat, and avk.dll.
Security teams should also review outbound traffic for the fake Claude domains and the reported command-and-control IP address. Sophos linked license[.]claude-pro[.]com to 8.217.190.58.
Businesses should treat this campaign as another reminder that AI tools have become high-value lures. Attackers know users are actively searching for new AI apps, desktop clients, browser extensions, and developer utilities.
FAQ
It is a Windows malware campaign that uses a fake Claude-themed website to distribute a malicious installer. The installer deploys DonutLoader and a backdoor named Beagle.
No evidence suggests the official Claude website was compromised. The attack used a separate fake domain that impersonated Claude.
DLL sideloading lets attackers abuse trusted programs to load malicious DLL files. This can help malware blend in with legitimate software activity.
Beagle is a backdoor documented by Sophos in this campaign. It can receive remote commands, transfer files, manage directories, and maintain access to an infected system.
Summary
- A fake Claude website is spreading a malicious Windows installer.
- The installer uses DLL sideloading to launch DonutLoader.
- DonutLoader delivers Beagle, a newly documented Windows backdoor.
- The campaign resembles PlugX-style attack chains but uses a different final payload.
- Users should download Claude only from official Anthropic sources.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages