Popular Go Library fsnotify Triggers Supply Chain Concerns After Maintainer Access Dispute

A maintainer access dispute around fsnotify has raised supply chain concerns across the Go and Kubernetes communities. The widely used Go library did not show public evidence of a confirmed compromise, but the sudden governance changes created enough uncertainty for downstream projects to start reviewing the situation.
fsnotify provides cross-platform filesystem notifications for applications running on Windows, Linux, macOS, BSD, and illumos. That makes it a quiet but important dependency inside developer tools, command-line apps, infrastructure projects, and automation workflows.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
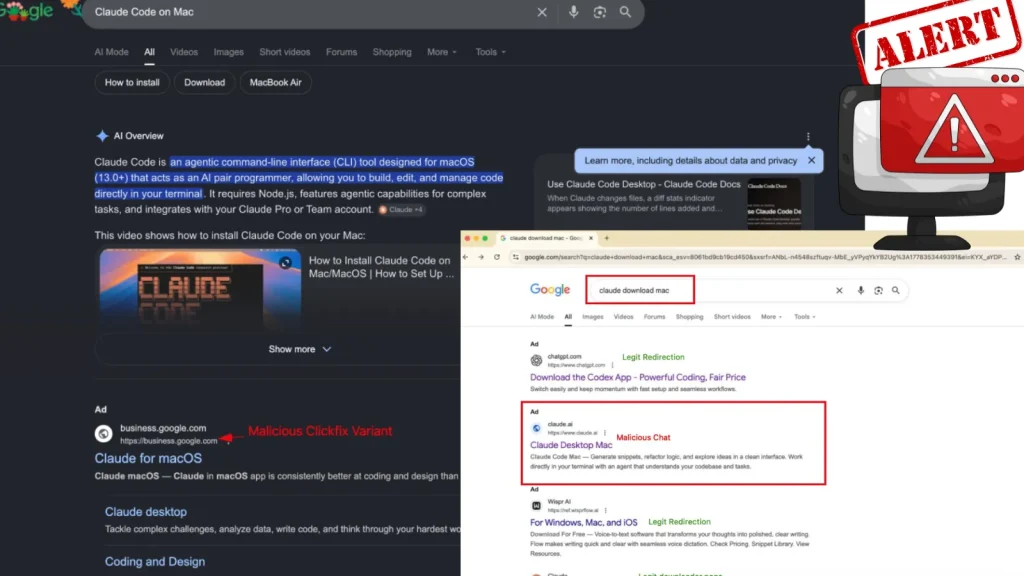
The concern started after contributors were removed from the project’s GitHub organization. From the outside, users could not immediately tell whether this was routine project cleanup, a maintainer dispute, or an early sign of a supply chain issue.
Why fsnotify drew so much attention
fsnotify matters because it sits low in the software stack. Many developers may not install it directly, but their tools and dependencies can still rely on it for file change detection.
Socket reported that the project had about 10.7K GitHub stars, 969 forks, and roughly 321K dependent projects. For a library with that reach, changes to maintainer access quickly become more than an internal project matter.
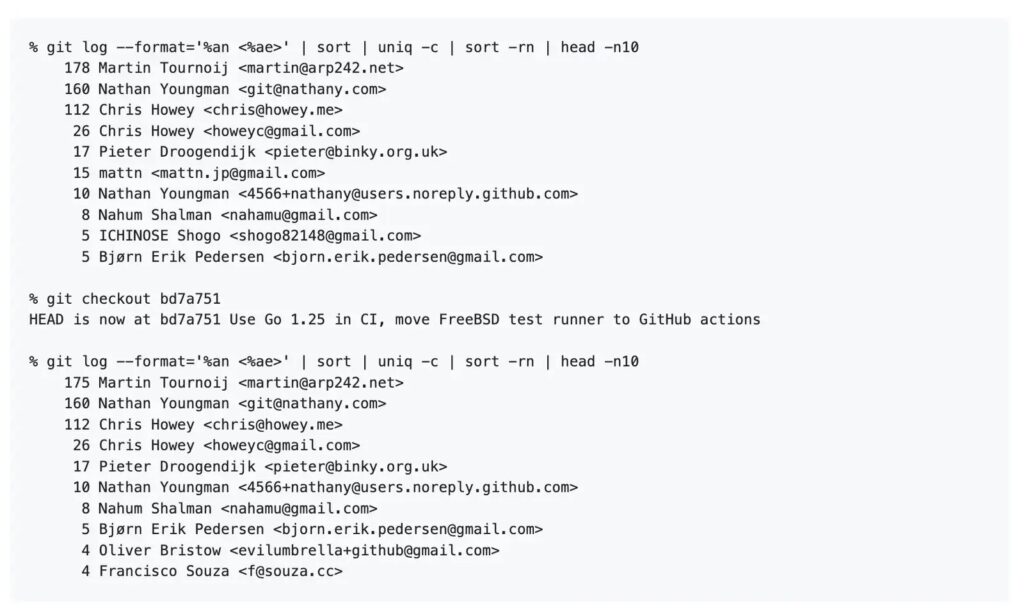
The concern intensified because recent releases had also appeared around the same period. fsnotify v1.10.0 was released on April 29, 2026, followed by v1.10.1 on May 4, 2026. Both releases were signed by Go developer Yasuhiro Matsumoto, known online as mattn.
What changed inside the project
The public dispute centered on why several accounts lost access to the fsnotify GitHub organization. Grafana Staff Developer Advocate Oshi Yamaguchi opened a GitHub issue asking for clear reasons, noting that fsnotify appears in major open source projects and that users needed enough context to assess risk.
Maintainer Martin Tournoij pushed back against the idea that the project had been hijacked. He argued that some users had commit rights for historical reasons but had not been active maintainers in a meaningful way.
Tournoij also said some recent changes moved too quickly and did not receive enough discussion or platform review. According to Socket’s summary of the thread, a sponsorship file update committed directly to the main branch became one of the triggers for revoking access.
Key facts at a glance
| Item | Details |
|---|---|
| Project | fsnotify |
| Language | Go |
| Main purpose | Cross-platform filesystem notifications |
| Supported platforms | Windows, Linux, macOS, BSD, illumos |
| Main concern | Maintainer access changes and unclear governance |
| Confirmed malicious release | No public evidence reported |
| Downstream reaction | Kubernetes contributors opened a tracking issue |
Kubernetes contributors started watching the situation
The issue quickly reached downstream projects. A Kubernetes GitHub issue titled “fsnotify/fsnotify – Healthy or not?” asked contributors to watch the project carefully and consider forks if needed.
The Kubernetes thread also pointed to gofsnotify/fsnotify, a separate repository created after the access dispute. Contributors noted that the naming similarity between the old and new repositories could confuse users if the dispute continued.
This does not mean Kubernetes confirmed a fsnotify compromise. It shows how major projects now react when a critical dependency enters a period of unclear ownership or unclear release authority.
Why this looked like a supply chain risk
Supply chain attacks often begin with changes that look ordinary at first. A new release, a maintainer change, or a shifted permission model may seem harmless until downstream users discover malicious code later.
The fsnotify case appears different because the public concern centers on governance rather than confirmed malware. Still, the pattern created understandable caution because developers have become more sensitive to changes in foundational open source projects.
The xz-utils backdoor from 2024 remains an important reference point for the industry. That incident showed how a trusted open source project can become a target when attackers gain influence over release paths.
What developers should check now
- Review which internal projects depend on fsnotify directly or indirectly.
- Check whether automated dependency tools recently opened fsnotify update pull requests.
- Review the release notes for v1.10.0 and v1.10.1 before upgrading.
- Pin versions in sensitive production environments until the team completes review.
- Monitor the official fsnotify repository and the Kubernetes tracking issue for updates.
- Avoid switching to similarly named forks without checking ownership, history, and code changes.
What this means for open source governance
The fsnotify dispute shows how much trust depends on maintainer clarity. A package can have clean code and still create security concern if users cannot understand who controls releases.
For widely used libraries, commit rights and release permissions need the same care as code changes. Projects with broad downstream usage should document who can merge, who can publish releases, and how access changes happen.
Clear governance does not prevent every dispute. It does reduce confusion when something changes, and it gives security teams a faster way to separate routine project maintenance from a real compromise.
FAQ
No public evidence shows that a fsnotify release was compromised. The concern came from maintainer access changes, recent releases, and unclear project governance.
fsnotify handles filesystem notifications for Go applications across major operating systems. Many tools rely on it indirectly, which increases the impact of uncertainty around the project.
There is no public evidence that developers must stop using fsnotify. Teams should review recent updates, monitor the official repository, and avoid rushed dependency upgrades in sensitive environments.
Kubernetes contributors opened a tracking issue because fsnotify is a widely used dependency and the maintainer access dispute raised questions about long-term project health.
Summary
- fsnotify triggered supply chain concerns after contributors lost GitHub organization access.
- No public evidence currently shows that fsnotify releases were compromised.
- The issue matters because fsnotify has a large downstream footprint.
- Kubernetes contributors opened a tracking issue and discussed watching forks.
- The incident highlights the need for clearer open source maintainer and release governance.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages