Vidar Malware Uses Fake Activation Tool to Steal Passwords, Cookies, and Crypto Wallets
A new Vidar malware campaign is using a fake software activation tool to steal browser credentials, session cookies, cryptocurrency wallet files, and system data from Windows machines.
LevelBlue researchers found the activity during proactive threat hunting in a client environment. Their analysis showed a multi-stage infection chain that uses script masquerading, staged payload extraction, security process checks, and command-and-control communication.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Vidar is not a new malware family. It has been active since late 2018 and was built from the source code of the older Arkei stealer. The latest campaign shows how attackers continue to wrap known infostealers in more evasive delivery chains.
Fake Microsoft Toolkit starts the infection
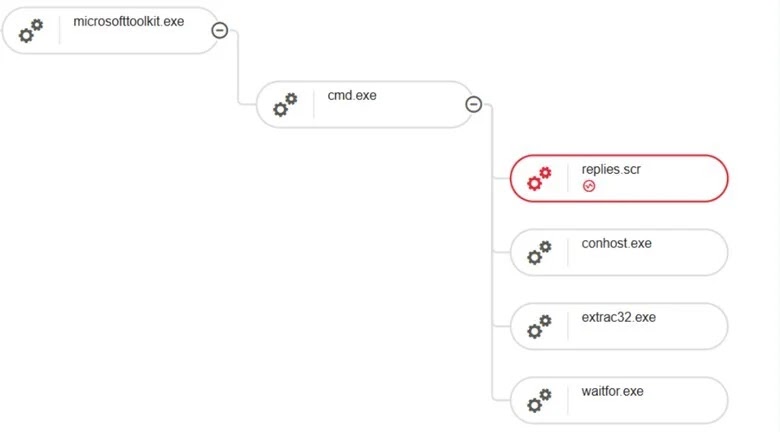
The attack begins when a user runs MicrosoftToolkit.exe, a commonly abused hack tool often presented as a software activation utility. This gives the malware a user-driven entry point instead of relying on a phishing attachment or browser exploit.
After execution, the tool launches a command shell and starts preparing the next stage. A disguised file named Swingers.dot is renamed into a batch script and executed.
This file extension trick helps the attack bypass simple security controls that block obvious script files. It also makes the chain look less suspicious during the early stage of execution.
Key facts at a glance
| Item | Details |
|---|---|
| Malware family | Vidar |
| Malware type | Information stealer |
| Initial file | MicrosoftToolkit.exe |
| Disguised script | Swingers.dot renamed as a batch file |
| Loader | Replies.scr, an AutoIt-compiled loader |
| Payload file | D |
| Main targets | Browser credentials, cookies, crypto wallets, and system data |
| Reported C2 indicators | telegram.me, Steam profile URL, and gz.technicalprorj.xyz |
The loader checks security tools before running Vidar
The batch stage uses Windows commands such as tasklist and findstr to look for running processes. This helps the malware identify security tools and analysis environments before it moves deeper into the infection chain.
The attack then uses extract32.exe to extract additional components and launches Replies.scr with an external payload file named D. Replies.scr is an AutoIt-compiled binary that acts as a loader instead of the final payload.
AutoIt is a legitimate Windows scripting language, but attackers often abuse it because compiled AutoIt programs can look like normal applications. In this campaign, AutoIt helps reconstruct and execute the Vidar payload through staged file manipulation.
Vidar targets data that attackers can reuse or sell
Once deployed, Vidar focuses on data that can quickly turn into account takeover, fraud, or follow-on attacks. It targets browser-stored credentials, saved session cookies, cryptocurrency wallet files, and user and system information.
Stolen browser cookies can be especially dangerous because they may let attackers access accounts without immediately needing the victim’s password. Wallet files can also expose cryptocurrency funds if attackers obtain the right supporting data.
On business systems, the risk can extend beyond one user. A stolen browser session, VPN credential, admin login, or cloud account token can give attackers a path into company systems.
Command-and-control uses common web services
LevelBlue observed Vidar-related communication using Telegram and a Steam profile URL. This kind of infrastructure abuse helps attackers hide configuration retrieval inside traffic that may look normal at first glance.
The malware also performed DNS activity tied to gz.technicalprorj.xyz. LevelBlue included this domain in its hunting guidance for defenders monitoring suspicious outbound traffic.
By using public platforms and web-based communication, attackers can make blocking harder. Security teams may hesitate to block large legitimate services entirely, so defenders need more precise detection based on process behavior and unusual connections.
The malware removes evidence after execution
The campaign includes a cleanup routine after the payload runs. LevelBlue said the malware deletes dropped files, resets attributes, frees memory, and terminates its own process.
This cleanup behavior complicates incident response because investigators may find fewer files on disk after the attack completes. It also reduces the chance that simple file-based detections will catch the full chain later.
The malware also uses anti-debugging and anti-analysis checks. These checks help it detect when researchers or security tools are watching execution and may cause it to change behavior.
What security teams should monitor
- Execution of MicrosoftToolkit.exe or similar unauthorized activation tools.
- Files renamed from .dot to .bat before execution.
- Unexpected AutoIt-compiled binaries such as Replies.scr.
- Command-line use of tasklist, findstr, extract32.exe, and waitfor.exe in the same chain.
- Outbound connections from unusual scripts or screensaver files.
- DNS lookups for gz.technicalprorj.xyz.
- Suspicious access to Telegram or Steam URLs from unknown binaries.
- Rapid file creation followed by deletion in temporary or user-controlled paths.
What affected users should do
Any system that executed this chain should be isolated from the network immediately. That helps stop further data theft and reduces the risk of lateral movement.
Organizations should reimage affected systems because Vidar can be used with additional payloads. Cleaning only the visible files may not remove every component or follow-on tool.
Users should reset browser passwords, email passwords, VPN credentials, cloud accounts, and administrator accounts from a clean device. They should also invalidate active sessions and enforce multi-factor authentication wherever possible.
FAQ
Vidar is an information stealer that targets credentials, browser data, cryptocurrency wallet files, cookies, and system information from infected Windows machines.
The campaign starts with MicrosoftToolkit.exe, a commonly abused software activation tool that tricks users into running the first stage manually.
Replies.scr is an AutoIt-compiled loader. It processes an external payload file and helps launch the Vidar stealer.
Stolen session cookies can help attackers access accounts without typing the password again, especially when the session remains active.
Summary
- Vidar malware is using a multi-stage Windows infection chain to steal sensitive data.
- The campaign starts with MicrosoftToolkit.exe and uses disguised .dot files, batch scripts, and an AutoIt loader.
- The malware targets browser credentials, session cookies, crypto wallets, and system data.
- Attackers use public platforms such as Telegram and Steam as part of command-and-control activity.
- Defenders should block unauthorized activation tools, monitor renamed scripts, and reimage infected systems.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages