Iranian-Nexus Hackers Hit Oman Ministries and Expose 26,000 Citizen Records

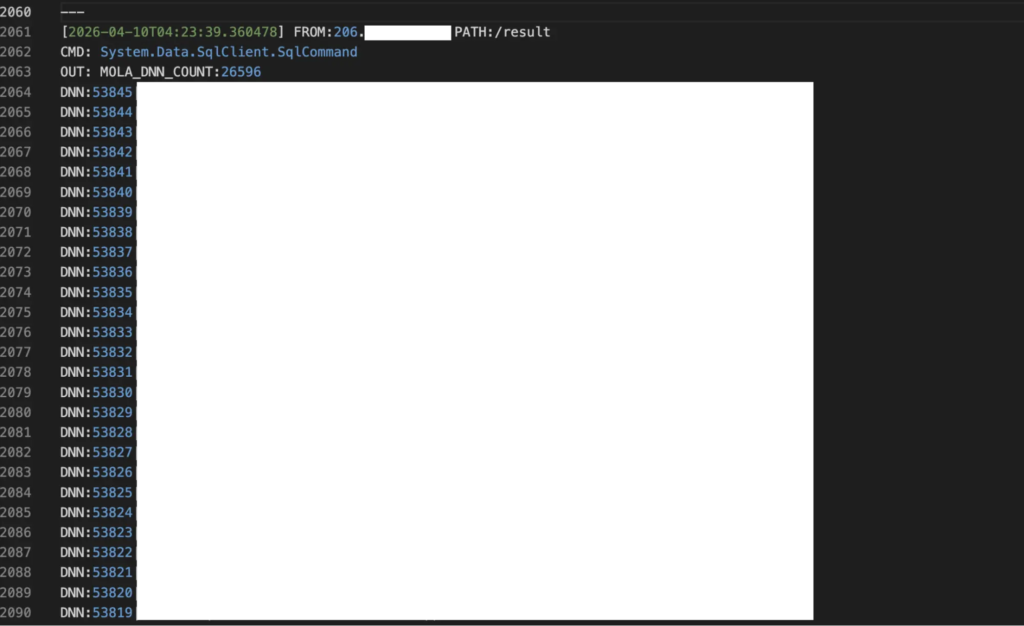
An Iranian-nexus cyber operation targeted Oman’s government ministries and exposed more than 26,000 citizen records, according to new threat research from Hunt.io. The campaign focused on government portals, judicial data, identity records, credentials, and internal systems used by public institutions.
The attackers used webshells, SQL escalation scripts, Exchange exploitation attempts, password spraying, and command-and-control infrastructure to move through the environment. The primary confirmed victim was Oman’s Ministry of Justice and Legal Affairs, where logs showed active operator activity on April 10, 2026.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign came to light because the attackers left a staging server exposed. Hunt.io found an open directory on a UAE-hosted RouterHosting VPS at 172.86.76[.]127, which revealed the toolkit, C2 scripts, session logs, stolen data, and targeting files.
What researchers found
The exposed server gave researchers a rare look at an active government intrusion. It contained 211 files, 17 directories, command scripts, exploit folders, PowerShell tooling, and a README file that described the system as “VPS C2.”
That label suggests the machine may have been one node in a larger setup. The files also showed a structured working environment rather than a loose collection of tools, which means the operators had organized the campaign across separate functions.
The campaign did not only target one ministry. Hunt.io said file names and attack scripts mapped to 12 Omani government entities, including the Ministry of Justice and Legal Affairs, Royal Oman Police, Tax Authority, Ministry of Finance, Civil Aviation Authority, and Office of Public Prosecution.
| Key detail | What was found |
|---|---|
| Main confirmed victim | Oman Ministry of Justice and Legal Affairs |
| Government entities targeted | 12 ministries and public bodies |
| Records extracted | 26,596 Ministry of Justice user records |
| Exposed infrastructure | UAE-hosted RouterHosting VPS at 172.86.76[.]127 |
| Confirmed operator activity | April 10, 2026, starting around 03:00 UTC |
| Attribution status | Iranian state-nexus activity, without formal group-level attribution |
Webshells gave attackers command access
Two webshells played a central role in the operation. One file, hc2.aspx, appeared on the exposed C2 server. Another webshell, health_check_t.aspx, appeared hardcoded across attack scripts that targeted the Ministry of Justice environment.
The webshells let the attackers pass commands to Windows command processes and receive output as plain text. In practice, this gave the operators a way to run discovery commands, check host details, query databases, and continue working inside the compromised network.
Hunt.io also found scripts that pointed to a possible DotNetNuke attack path. CVE-2025-32372 affects DNN, formerly DotNetNuke, and can allow semi-blind server-side request forgery against vulnerable systems. The flaw was fixed in DNN 9.13.8.
What data was stolen
The stolen data appears especially sensitive because it involved government, identity, and judicial systems. Hunt.io said the attackers extracted Ministry of Justice user records, judicial case data, committee decisions, expert certification data, and Windows registry hives.
The database activity showed a clear interest in user accounts and identity information. The attackers queried DotNetNuke membership tables, looked for superuser accounts, and tried to collect stored credentials that could help them expand access.
Some queries also targeted personal data, including national ID numbers, full names in Arabic and English, dates of birth, and nationality records. This kind of data can support espionage, identity abuse, phishing, and long-term targeting of government employees or citizens.
- Ministry user records
- Judicial case data
- Committee decision files
- Expert certification information
- National identity records
- Windows SAM and SYSTEM registry hives
- Internal credentials and account data
The campaign reached beyond one agency
The exposed files showed targeting across a wide part of Oman’s public sector. The Royal Oman Police eVisa portal appeared in brute-force activity, while Royal Fleet of Oman and Tax Authority mail servers appeared in ProxyShell-related scripts.
The Office of Public Prosecution was linked to SQL injection and database extraction activity. The Ministry of Finance appeared in scripts linked to Spring Boot Actuator exposure, while other portals were tied to enumeration, authentication probing, and application-level attacks.
Researchers also found a dedicated gov[.]om folder with 12 exploit scripts. These covered Exchange spraying, SQL Server escalation, memory-based execution, Oracle APEX and ORDS attacks, WAF bypass attempts, Fortinet checks, Joomla targeting, and national ID access weaknesses.
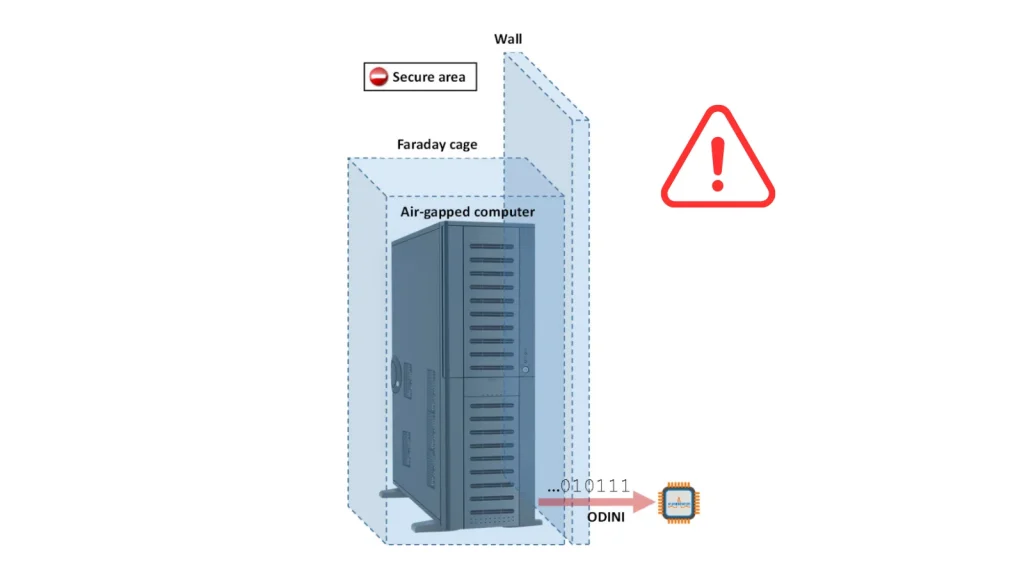
Command-and-control setup and persistence
The C2 system used Python HTTP server code and a PowerShell beacon on the victim side. The beacon checked in every 30 seconds and sent the victim domain, username, and hostname at the beginning of each session.
Stolen data moved back in small encoded chunks. This helped the attackers avoid simple URL length limits while still sending data through command-and-control traffic.
The operators also attempted persistence with a scheduled task named MicrosoftEdgeUpdate. Microsoft Defender blocked that attempt, but another script on the exposed server showed an effort to disable antivirus protection.
Why researchers connect it to Iranian-nexus activity
Hunt.io placed the campaign in the broader Iranian state-nexus space, but it did not assign the activity to a specific group. The reason is important: strong attribution needs unique malware, shared infrastructure, or other firm technical links.
The operation still overlaps with known Iranian-nexus patterns. Hunt.io noted similarities with APT34, also known as OilRig, and MuddyWater, also known as Mango Sandstorm. Those overlaps include regional government targeting, PowerShell-heavy tooling, Chisel use, ProxyShell-related activity, and credential-focused operations.
The surrounding infrastructure also added context. Neighboring systems in the same hosting cluster included domains tied to Iranian-language content, censorship circumvention themes, and other services. Hunt.io treated these as useful context, not final proof of one specific group.
Why this matters for government security
This incident shows how old vulnerabilities and weak portal security can still support serious intrusions. ProxyShell dates back to 2021, yet the files suggest attackers still test Exchange servers for exposure when hunting government networks.
The campaign also shows why exposed attacker infrastructure matters. A single open directory revealed how the operators worked, which organizations they targeted, which files they collected, and how they moved data out of the victim environment.
For defenders, the main lesson is direct. Government agencies need to monitor internet-facing servers, patch old public-facing systems, review webshell indicators, audit identity portals, and watch for unusual PowerShell and SQL Server behavior.
Indicators highlighted by researchers
| Indicator | Associated domain or note | Hosting |
|---|---|---|
| 172.86.76[.]127 | dubai-10.vaermb[.]com | RouterHosting LLC, UAE |
| 172.86.76[.]101 | dubai-1.vaermb[.]com, regorixa[.]com | RouterHosting LLC, UAE |
| 172.86.76[.]108 | dubai-3.vaermb[.]com, myjitsi.exceptionnotfound[.]ir | RouterHosting LLC, UAE |
| 172.86.76[.]124 | suanefllix[.]com, brnettlix[.]com, realprimefix[.]com | RouterHosting LLC, UAE |
| 45.59.114[.]60 | shop.exceptionnotfound[.]ir, myjitsi.mrnajafipour[.]ir | RouterHosting LLC, Switzerland |
| 104.21.27[.]95 and 172.67.142[.]35 | tools.exceptionnotfound[.]ir | Cloudflare |
FAQ
The primary confirmed victim was Oman’s Ministry of Justice and Legal Affairs. Hunt.io also found files that mapped to 12 Omani government ministries and public bodies.
Researchers found evidence that 26,596 Ministry of Justice user records were extracted from the compromised environment.
The attackers used webshells, PowerShell beaconing, SQL Server escalation, ProxyShell-related scripts, credential attacks, and post-compromise tooling such as GodPotato.
No. Hunt.io connected the activity to the broader Iranian state-nexus space, but it did not make a formal group-level attribution.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages