Fake Claude AI installer pages are tricking users into running malware
Hackers are using fake Claude AI installer pages to trick Windows and macOS users into running malware commands on their own systems. The campaign, known as InstallFix, targets people searching for Claude Code installation instructions and uses sponsored search results to make malicious pages look trustworthy.
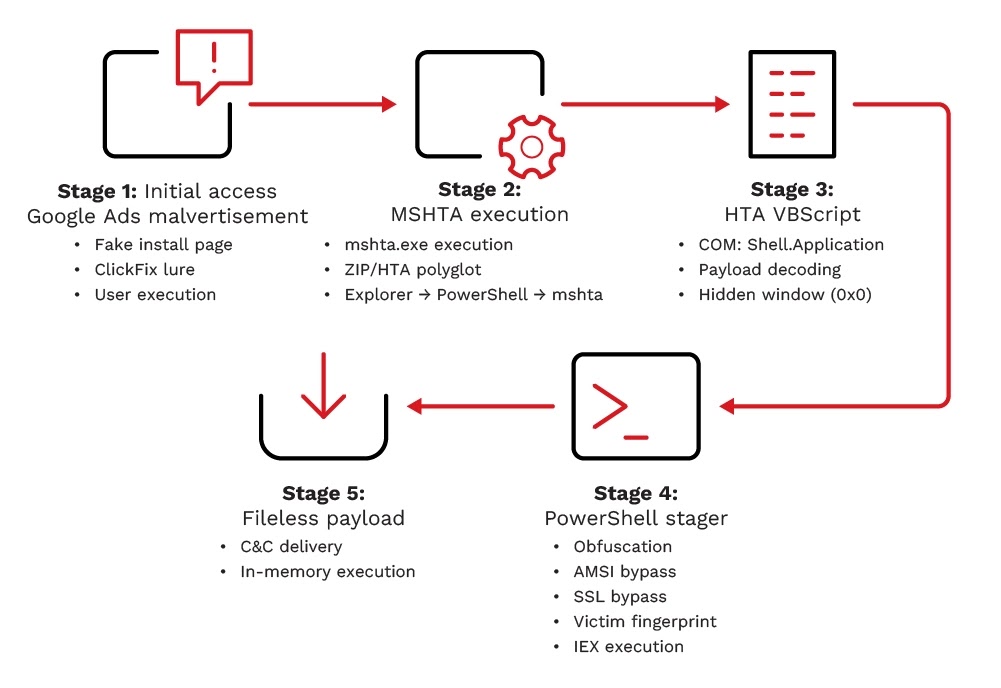
The attack does not rely on a software vulnerability. It relies on users copying and running commands from a page that looks like official documentation. Once the command runs, the system starts a multi-stage infection chain that can collect system data, disable security protections, create persistence, and connect to attacker-controlled servers.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Trend Micro says the campaign has targeted organizations in the United States, Malaysia, the Netherlands, and Thailand. Observed industries include government, education, electronics, and food and beverage.
How the fake Claude installer attack works
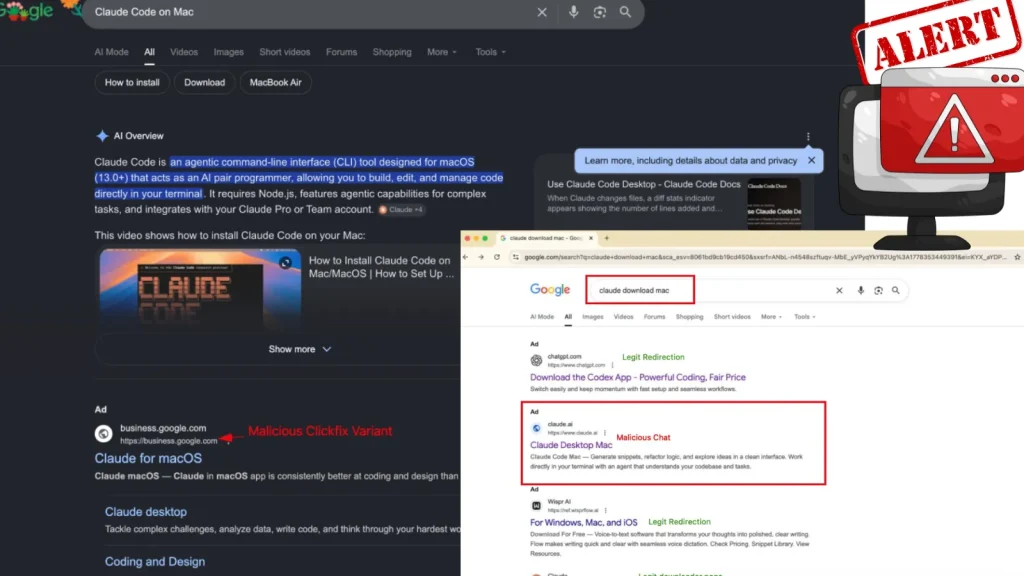
The campaign begins when users search for terms such as Claude Code or Claude Code install. Attackers place sponsored search results that lead to fake installation pages designed to resemble real Claude documentation.
The page detects or presents instructions for the visitor’s operating system. Windows users receive commands that abuse legitimate Windows tools, while macOS users see terminal-style instructions that appear normal for developer tools.
This makes the lure effective against both technical and non-technical users. Developers often expect command-line installation steps, while less experienced users may trust the instructions because the result came from a sponsored search placement.
At a glance
| Item | Details |
|---|---|
| Campaign name | InstallFix, also called the Fake Claude Installer threat |
| Main lure | Fake Claude AI and Claude Code installation pages |
| Distribution method | Sponsored search results and malvertising |
| Targets | Windows and macOS users searching for Claude Code setup instructions |
| Initial execution | User runs a command copied from the fake page |
| Observed impact | System profiling, security bypass attempts, persistence, data theft, and command-and-control activity |
| Reported regions | United States, Malaysia, Netherlands, and Thailand |
Why the campaign is convincing
Claude Code is a legitimate developer tool, and its real installation process can involve command-line steps. Attackers exploit that expectation by copying the look of documentation pages and replacing trusted commands with malicious ones.
The fake pages use the same habit many developers already follow: copy a command, paste it into Terminal or PowerShell, and press Enter. That habit becomes dangerous when users trust the wrong page.
Some fake pages also use links and layouts that make the site look more credible. The URL is often the only clear warning sign, and many users do not check it closely before running a command.
What happens on Windows systems
On Windows, Trend Micro observed PowerShell invoking mshta.exe to download and execute a malicious payload disguised as claude.msixbundle. Mshta.exe is a legitimate Microsoft utility, but attackers often abuse it to run remote HTML application payloads.
The downloaded file uses a deceptive package format and hides script execution behind what appears to be an installer. The infection chain then launches obfuscated commands and continues loading the next stages.
The malware can create a unique victim identifier by hashing the computer name and username. It then uses that identifier to build a victim-specific command-and-control URL, which makes broad blocking harder for defenders.
What happens after infection
| Stage | What the attacker does | Security impact |
|---|---|---|
| Initial access | Uses sponsored results to send users to a fake Claude installer page | Bypasses normal suspicion through familiar branding |
| Command execution | Tricks users into running OS-specific commands | Turns the user into the execution step |
| Payload delivery | Downloads a disguised package or script from attacker infrastructure | Starts a multi-stage infection chain |
| Evasion | Uses obfuscation, fileless execution, and security bypass techniques | Makes detection and analysis harder |
| Persistence | Creates scheduled tasks or similar mechanisms | Allows malware to survive reboots |
| Command and control | Connects to attacker-controlled servers for more instructions | Gives attackers a path for further payloads and data theft |
Why developers face higher risk
Developers often install tools from documentation pages and run setup commands in terminals. That normal workflow creates an opening for attackers who can clone documentation and buy search ads.
The risk also extends beyond the infected device. A developer workstation may hold source code, API keys, SSH keys, cloud sessions, browser tokens, package manager credentials, and access to internal repositories.
If an infostealer reaches those assets, attackers may move from one infected workstation to cloud systems, code repositories, CI/CD pipelines, and internal applications.
Observed indicators from the campaign
| Indicator type | Indicator | Context |
|---|---|---|
| Domain | download-version[.]1-5-8[.]com | Used to host the fake claude.msixbundle payload |
| Domain | oakenfjrod[.]ru | Command-and-control domain using victim-specific subdomains |
| File name | claude.msixbundle | Malicious payload disguised as a Claude AI installer |
| File name | Claude.msixbundle.zip | Archive containing an obfuscated script payload |
| SHA256 | 2f04ba77bb841111036b979fc0dab7fcbae99749718ae1dd6fd348d4495b5f74 | Hash tied to a recovered later-stage payload |
| IP address | 104[.]21[.]0[.]95 | Outbound command-and-control activity observed during analysis |
| IP address | 185[.]177[.]239[.]255 | Outbound command-and-control activity observed during analysis |
| IP address | 77[.]91[.]97[.]244 | HTTPS traffic observed during analysis |
Why sponsored search results create trust
Many users assume a sponsored search result has passed a stronger trust check. That assumption gives attackers an advantage when they impersonate popular AI tools.
Google’s advertising policies prohibit malware and attempts to trick or bypass review systems, but malicious campaigns still appear when attackers abuse advertiser accounts, redirects, compromised infrastructure, or convincing landing pages.
This means users and companies cannot rely on search placement alone. The safer approach is to visit official vendor pages directly, bookmark trusted documentation, and avoid running commands from ads or unfamiliar domains.
How organizations can reduce risk
- Block known malicious domains and IP addresses from the campaign.
- Use DNS filtering to block newly registered and suspicious domains.
- Restrict mshta.exe where business operations do not require it.
- Monitor PowerShell, Terminal, curl, bash, and mshta.exe activity for unusual download behavior.
- Train users to avoid running install commands from sponsored search results.
- Tell developers to use official vendor documentation, package registries, and verified repositories.
- Review browser-stored credentials, cookies, API keys, and developer tokens after suspected infection.
- Use endpoint detection rules for scheduled task creation after suspicious command execution.
What users should do before installing Claude Code
Users should go directly to the official Claude Code documentation or trusted package sources before installing the tool. They should also check the domain carefully before copying any command into a terminal or command prompt.
When possible, users should prefer known package managers or vendor-published installation methods instead of commands from search ads. They should also read the command before running it, especially if it downloads and executes a remote script.
Organizations should publish approved internal instructions for installing AI developer tools. This reduces the chance that employees will search the web and land on a malicious clone.
FAQ
Yes. Researchers observed fake installer instructions for both Windows and macOS users.
It is a malvertising and social engineering campaign that uses fake Claude AI or Claude Code installer pages to trick users into running malware commands.
InstallFix is a social engineering method where attackers clone software installation pages and replace legitimate setup commands with malicious ones.
No. The campaign abuses trust in Claude branding and developer installation habits. The infection starts when a user runs commands from a fake page.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages