Can WireGuard Be Obfuscated? & How To Do It Step-By-Step
Disguise, encrypt, and secure your online presence against censorship and surveillance.
Can WireGuard Be Obfuscated? Yes, but there’s a catch: it doesn’t have the built-in option, so you’ll need additional tools. I’ll lay it all down for you.
As a VPN user, you probably noticed that most VPN services offer obfuscation via OpenVPN. But what if you prefer WireGuard for its unmatched speed? Well, you can hide its traces just as good, but it takes some extra steps. Follow them below.
Can WireGuard be obfuscated?
Yes, WireGuard can be obfuscated, although it’s important to note that obfuscation is not a built-in feature of the protocol itself; you’ll need additional tools after setting up WireGuard.
The most common technique is integrating with Shadowsocks. Other options include routing traffic through a proxy or tunneling protocol like SSH, changing ports (e.g., to 443), or developing custom solutions for highly restrictive environments.
Find below how you can obfuscate WireGuard yourself.
How to obfuscate WireGuard?
Here’s how you can create WireGuard traffic obfuscation:
Use Shadowsocks
Here’s a step-by-step guide on how to obfuscate WireGuard traffic using Shadowsocks:
- Choose a VPN plan and register an account with a VPN provider.
- Download the Wireguard configuration file.
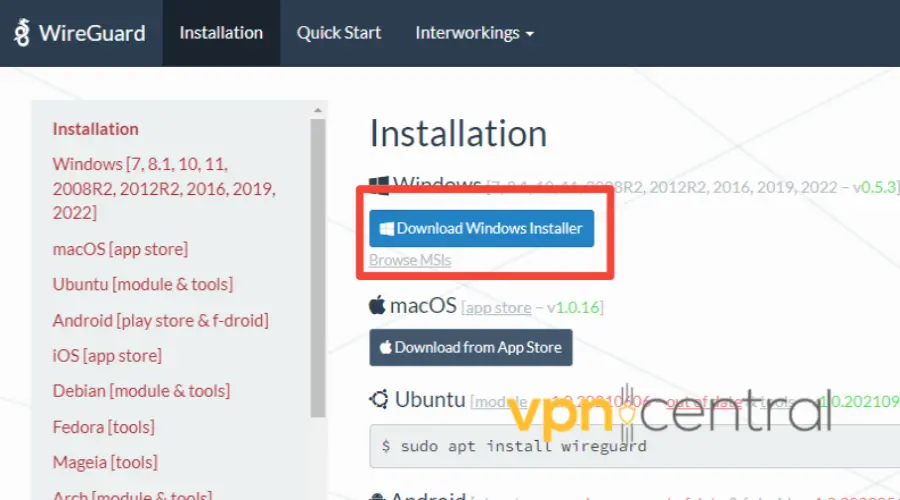
- Install the latest Wireguard Windows installation package from the Wireguard website. Alternatively, you can also install it on Linux, macOS, or even Android, if that’s what you use.
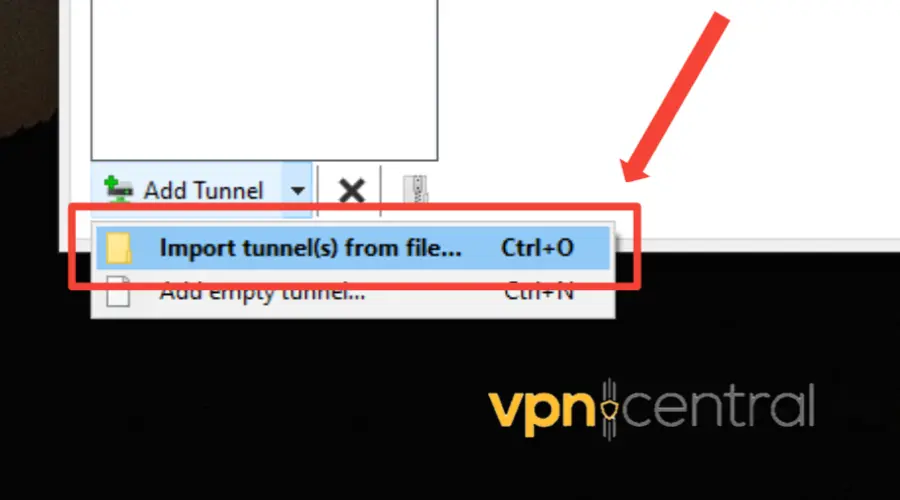
- Launch the Wireguard client and navigate to Add Tunnel u003e Import Tunnel from File.
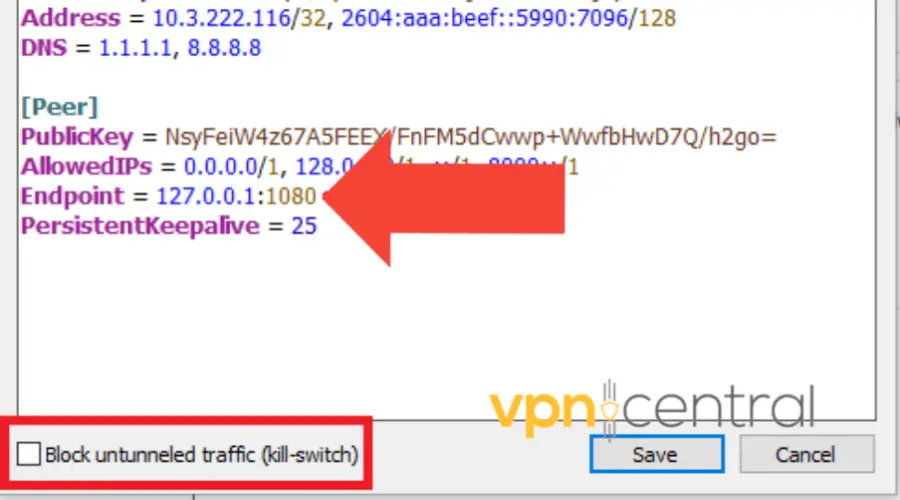
- Edit the configuration by modifying the Endpoint to 127.0.0.1:1080 and disabling the Block untunneled traffic option.
- Create a local directory and download the Windows shadowsocks sslocal.exe executable and the configuration file to connect to the VPN provider’s server.
- In the directory, enter the following command: sslocal.exe c- shadowsocks-client-config.json
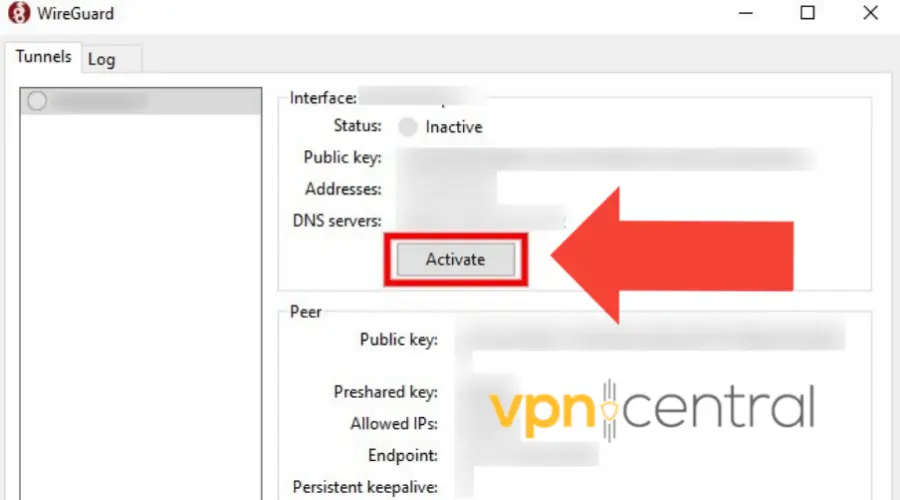
- Connect with Wireguard by clicking the Activate button. You’ll connect to the VPN provider’s Wireguard VPN via Shadowsocks obfuscation.
Note: If you encounter any issues, such as IP errors or connection issues, try removing the IPv6 configuration in the configuration file.
Nevertheless, Shadowsocks is a popular proxy tool that uses various obfuscation techniques to disguise traffic as normal web traffic.
It’s often used in countries with heavy internet censorship. That’s because it can effectively bypass deep packet inspection and other forms of censorship.
Other obfuscation methods
Shadowsocks will tunnel WireGuard traffic over an obfuscated SOCKS5 proxy, making the traffic information you send seem like regular traffic.
But there are other ways to go about it, although they’re not as easy to configure and not as reliable either.
- UDP2RAW will convert WireGuard traffic to UDP with an obfuscation layer that looks like normal UDP traffic.
- Stunnel allows you to encrypt arbitrary TCP connections and tunnel them through an SSL/TLS interface
- Change Ports to Mimic HTTPS Traffic
- Edit WireGuard Configuration
- Open your WireGuard configuration file (wg0.conf or similar).
- Change the ListenPort to 443 (common HTTPS port).
- Adjust Firewall Settings
- Update any firewall rules to allow traffic on port 443.
- Restart the WireGuard service to apply changes.
- Edit WireGuard Configuration
What does obfuscation do?
Obfuscation acts as an additional layer of encryption that conceals the actual VPN. So not only is your activity encrypted and private, but the very fact that you use a VPN is hidden.
Its purpose is to randomize internet traffic to make it appear as standard traffic, which can help it bypass VPN firewalls.
Technically, ISPs and governments can use deep packet inspection tools to identify the VPN protocol and confirm that you’re using VPN.
However, WireGuard obfuscation can jumble up the connection metadata and disguise the traffic as regular internet traffic.
While obfuscation can enhance online privacy and security by allowing users to bypass censorship and surveillance measures, it’s important to note that it may slow down your connection.
Read more:
Summary
Obfuscation makes it difficult for countries with strict internet censorship, VPN-blocking streaming services, or ISPs to detect you’re using a VPN.
Obfuscating WireGuard is not only possible, but it will enhance your online privacy.
It helps to mask the VPN traffic, making it difficult for third parties to detect and block it.
Also, there are different obfuscation tools available for WireGuard, and users can choose the one that suits their needs and requirements.
By following the steps discussed in this article, you can obfuscate your WireGuard.
Ultimately improving privacy and security.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
1 messages