Is Torrentz2 Safe? [Everything You Need to Know]
Torrentz2 is a well-known search engine for torrent files that offers users access to an extensive collection of torrents.
Its establishment came as a replacement for Torrentz, which was shut down in 2016.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
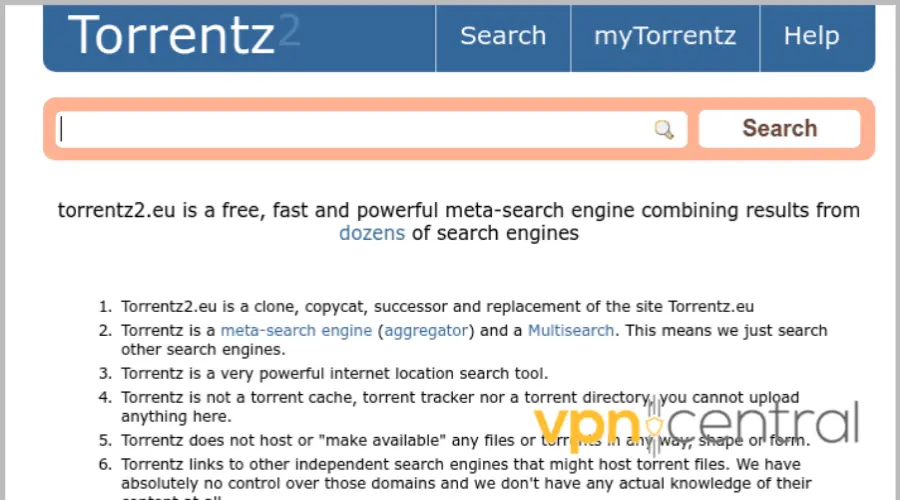
However, Torrentz2 does not host torrent files on its servers but simply provides users with links to websites where the files can be downloaded.
Therefore, because they have several sources, it’s natural to ask the question, is torrentz2 safe?
Table of contents
Is torrentz2 safe?
No, Torrentz2, like most torrent sites, can expose users to security and privacy risks depending on the content being shared and the source of the torrent files.
For example, a user gave a review of malware invasion when using torrentz2 for downloading.
Therefore, it is essential to exercise caution and take necessary precautions to stay safe when using Torrentz2.
Here are potential risks a user can experience on Torrentz2:
? Malware & virus risk
Hackers thrive best on torrent websites, generally speaking.
For the public to download executable files and apps, hackers insert malware such as Trojans, RATs, Rootkits, Ransomware, Spyware, Keyloggers, and many others.
The malware automatically runs once you download and launch such files or apps, initiating various data modification operations.
These files can destroy your data or render your system completely unusable. But you can keep your device safe by screening all downloaded files with powerful antivirus software.
?⚖️ Legal Issues
Most torrent downloads contain stolen paid content, which is one of the most significant risks of utilizing torrents.
However, piracy is seen as a crime and a kind of intellectual property theft in many nations.
Currently, copyright authorities and surveillance agencies are always watching torrent users; if they catch them, they could be prosecuted.
? ISP tracking
ISPs may monitor and throttle the internet speed of users who engage in torrenting activities to reduce network congestion and comply with copyright laws.
Also, some ISPs may block access to torrent sites altogether, preventing users from accessing these sites.
?️ Data safety
Unprotected content downloads from Torrentz2 or any other torrent website can pose a phishing attack by creating a fake torrent file.
This file contains a link to a fake website that asks for your login credentials, credit card information, or other personal information.
How to stay safe on torrentz2?
We’ll show you how to stay safe on torrentz2 but keep in mind that we do not support copyright violation or restriction evasion, including downloading illicit material or using torrents.
However, there are many possibilities to engage in safe and legal online torrenting, but torrenting is a terrific way to access and distribute all kinds of content online.
Therefore, we advise you to research whether these services and torrents are legal in your country.
Here are some tips to help you stay safe when using Torrentz2:
1. Use a VPN
A VPN transmits all data through a different server while encrypting your internet connection. Apps and websites cannot identify the actual traffic source as a result.
Therefore, you can avoid geo-restrictions by choosing the server location using a reputable VPN.
As an example, consider Private Internet Access VPN. It is one of our top suggestions for keeping users safe on Torrentz2.
Here’s how to torrent using a torrentz2 VPN:
- Visit PIA’s website and choose a subscription.

- Download the relevant VPN app on the device you wish to use to download torrent on torrentz2 and log in.
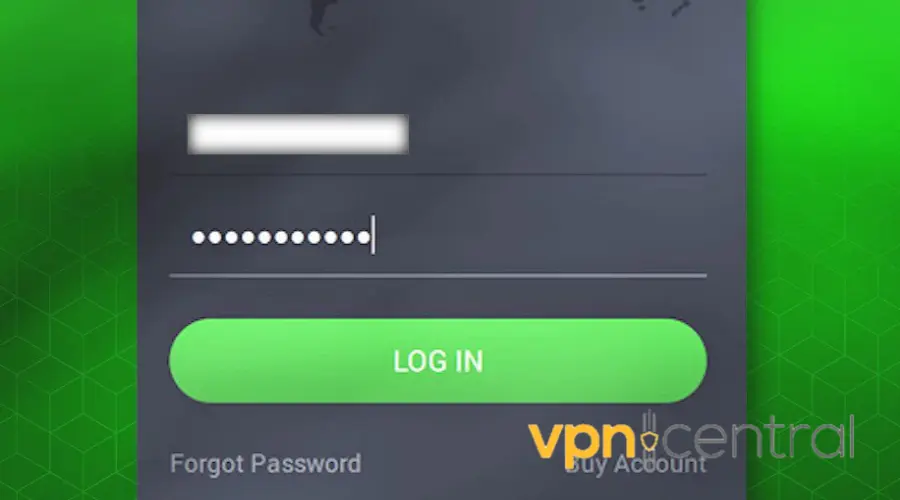
- Launch the VPN, search and select a location (New Zealand, for example). The default location is usually the fastest, but you can manually choose a different server if required.

- Once connected, go to Torrentz2 safely to download.

Private Internet Access
Protect your data and stay anonymous when torrenting using this P2P-friendly VPN!2. Protect privacy with a proxy server
Proxy services can sneak past firewalls and mask the user’s IP address by routing all internet queries through a different server.
You may download torrents anonymously using proxies, although they don’t offer the same level of privacy as VPNs.
A proxy must be manually set up in your torrent client’s settings to function effectively, unlike a VPN.
Here is how to set up a proxy on a torrent client, taking BitTorrent as an example:
- Open the BitTorrent client.
- Click Options and select Preferences from the menu.
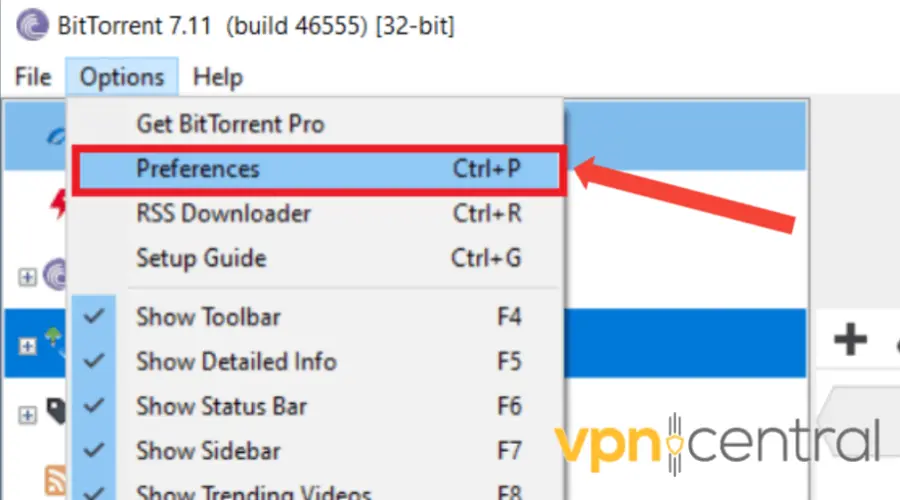
- Go to Connection.
- In the Proxy Server section, select Socks5 under Type.
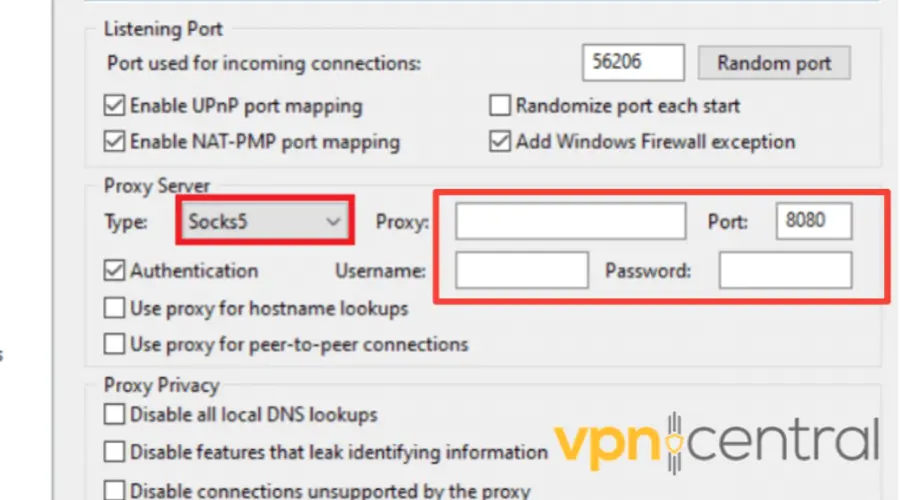
- In the Proxy field, enter the IP address of the proxy server you want to use. Then, in the Port field, type the port number. You will get this information from your proxy service provider.
- Check the Authentication field, and enter the proxy username and password you chose at signup.
- To avoid IP leaks, check the two options: “Use proxy for hostname lookups” and “Use proxy for peer-to-peer connections.”
- Also, check everything under Proxy Privacy.
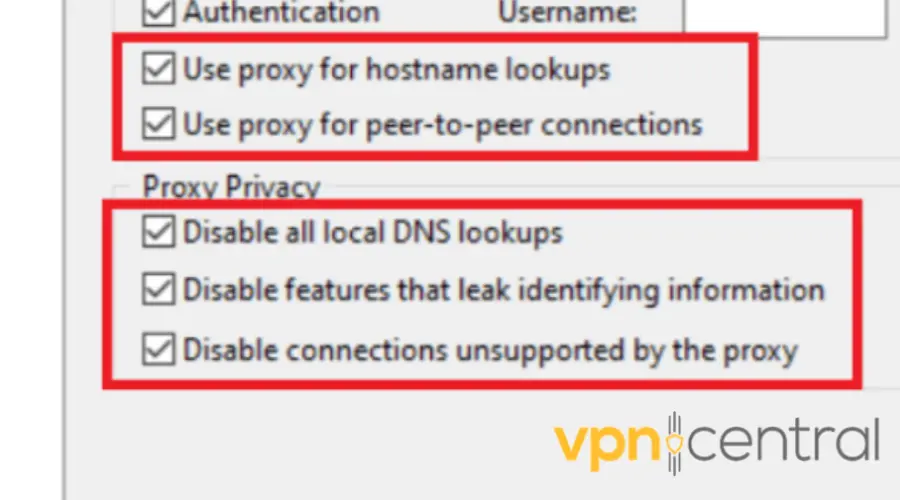
- Click on OK, and restart your BitTorrent client.
Although other proxy types exist for various use cases, HTTP and SOCKS5 proxies are the most frequently employed. And they’re far better for torrenting.
Conversely, SOCKS5 proxies are low-level “all-purpose” proxies that can easily handle any application, protocol, or internet traffic.
3. Use an efficient antivirus
For the best defense against malware, hackers, and online assaults, you should always have high-quality antivirus software installed on your computer.
The importance of this increases if you plan to download torrents because you’ll be exposing your device to connections from other sources, some of which can be malicious.
The antivirus will monitor and check any files you download and notify you immediately if any files contain malware.
Conclusion
Torrentz2 can be a helpful tool for finding and downloading files.
However, it is not secure if it is not adequately guarded against potential malware invasion, data theft, personal identity risk, and legal difficulties.
Therefore, VPNs and proxy services can make your time on Torrentz2 safer, especially when combined with powerful antivirus software and ad blockers. If you’re interested in safe access methods beyond Torrentz2, this detailed guide on using a LibGen proxy shows how proxies help bypass restrictions while protecting privacy.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages