How to Hide IP Address & Why It's a Good Idea

Your IP address reveals many things about you, including your approximate location and who’s your internet service provider.
In the wrong hands, this data can do a lot of damage, as skilled hackers and trackers can use it to dig in more and find a lot of sensitive information about you.
Apart from that, most blocked sites, games, and applications use your IP address information to enforce the block.
That’s equally true for IP blocks and geo-restrictions.
There are many other dangers apart from this, and that’s exactly why you need to protect yourself. For this reason, you’ll learn all you need to protect your IP.
Here’s what you’ll learn in this article:
- What is an IP address
- Why hide your IP
- How to hide the IP
- What are the dangers of not securing your IP?
So, let’s start.
What is an IP address and what does it do?
An IP (Internet Protocol) address is a string of numbers that you receive as soon as you connect to the web.
It serves as your online signature, and whenever you access any website, server, or anything else, the first thing it’ll do is scan your IP.
So there’s a record of everything you do online, based on your IP.
Through IP websites, hackers, ISP and even your government can track you.
Why do you need to hide your IP?
As we mentioned, IP addresses serve as your online signatures. We have said before that they are strings of numbers. But they are not random numbers.
Protect your identity
Every part of an IP carries some sort of information about its user. One part contains your location, another your ISP.
Now, would you like something with that sort of data publicly available?
Probably not.
Keeping your IP hidden not only keeps your navigational data private, but it also prevents spoofing and doxxing. Using VPN to hide IP is a great choice even to protect online security of your dear ones, especially on social media apps such as BeReal.
If you’re a fan of torrenting, things get even worse Why? Your IP will appear in the list of peers to everyone else that downloads the same content.
It’s not hard for someone with some skill to track you down and discover quite a bit about you if you’re running around the web with your IP wide open. Attackers may even use Angry IP Scanner alternatives or similar tools to scan for vulnerabilities and exploit weak points.
Bypass restrictions and censorship
There are other reasons as well, though. For example, geo-restrictions.
We’ll show you below how changing your IP will help you bypass them and other types of internet censorship.
We’ll describe how to do this and more, later in this guide.
How to protect your IP address?
Now that you have a clearer picture of the dangers of the internet, as well as the dangers of an unprotected IP, let’s see what we can do about it
First of all, you can change your IP and there are multiple ways to do it
1. Request an IP change from your ISP
If you have a static IP address, you’ll have to ask your ISP to change it for you, which might lead to a lot of awkward questions.
This will stop linking all your activity to the same IP address But it will not let you bypass restrictions
On the other hand, if your IP is a dynamic one, it will most likely change itself every time you connect to the internet. But as we said, this doesn’t help much.
Your ISP is only going to offer IPs from your area. So bypassing geo-blocks is out of the question.
There are better solutions out there, and those involve hiding your address, or at least masking it.
These are the solutions that work best and also allow you the most access to all of the restricted content. That’s why we are going to focus on those, and on how to do it, so let’s start with that.
2. Use a VPN to hide your IP
Using VPNs is the best method to mask your IP address online.
Doing it is one of the main reasons why VPNs exist, and the process itself is pretty simple but does a lot to help you.
The first thing that you need to know is what VPNs are.
VPN stands for Virtual Private Network, and they’re just that – private networks that consist of a lot of servers, scattered around the world.
Every VPN has its own set, placed in different locations.
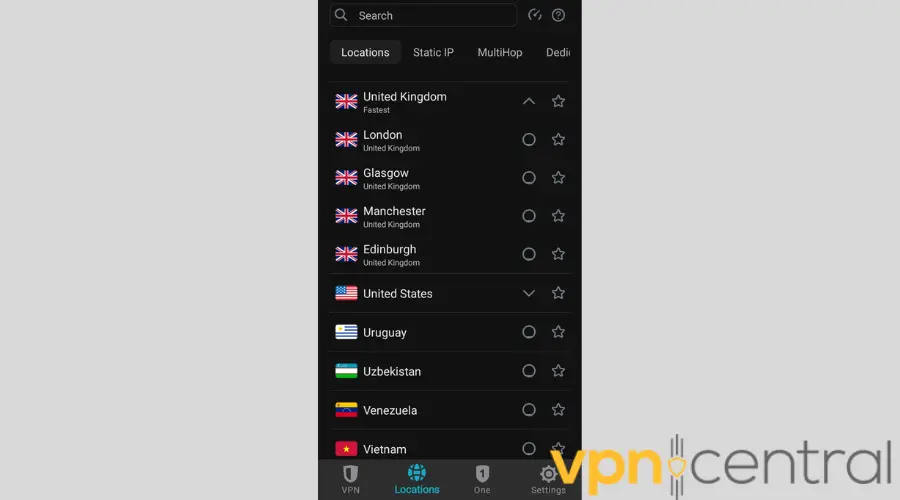
→ When you connect to the internet via VPN, you get to connect to one of these servers.
Once you choose which one you wish to use, it will give you an alternate IP address, one belonging to the region in which the server itself is located.
So basically, if you’re located in Europe, but you want to watch Hulu, that’s only accessible to those within the USA, you can use your VPN.
Just choose a US server, get a US IP address, and fool Hulu into thinking that you’re within the country’s borders.
The best thing about VPNs is that they cover your entire connection. So everything you do online once you connect is hidden.
This is also important because the second biggest reason for VPNs’ existence is their ability to encrypt your data by sending it through a secure tunnel.
With this ability, they can completely protect your online actions, and nobody else will be able to know what you do during your browser sessions.
They also offer many different features, like kill switches, which are important for keeping you secure.
If your VPN breaks down, your real IP might be exposed.
Kill switches will constantly cut your connection if something like this happens, and keep you safe and anonymous.
Other things that reliable VPNs offer include:
- no logging policy
- money return policy
- DNS leak protection
- obfuscation mode to bypass VPN blocks
- anti-tracking features
In our experience as avid VPN users and reviewers, you won’t go wrong if you use ExpressVPN, CyberGhost, or PIA.
Now, for a good and quality service, you’ll need to pay a monthly fee. Unfortunately, there’s no such thing as a really good and free VPN.
There are some solid free options, but they have a lot of limitations in terms of data and features.
Even worse, some free VPNs log and sell your data, which kind of defeats the whole purpose of using such a tool.
How to set VPN up?
Setting VPN up is actually a very short and easy procedure.
The first thing that you need to do is decide which VPN you wish to use. Upon deciding, you simply go to its website and sign up.
Next, you need to download and install the app, log into it, choose a server, and connect. That’s literally it. You’re now using a VPN, and your IP is completely hidden within the chosen server.
3. Hide your IP with a proxy
Proxies are another good way to hide IP addresses, but many would agree that they aren’t as good as VPNs.
Proxies don’t cover your entire connection, but rather only work with one piece of software, and they also don’t encrypt any of your data.
However, they’re an easier option that doesn’t slow you down as much as a VPN might.
Remember, VPNs encrypt all of your data, and that’s bound to take its toll on your speed.
However, a VPN makes your data totally safe and protected while a proxy doesn’t.
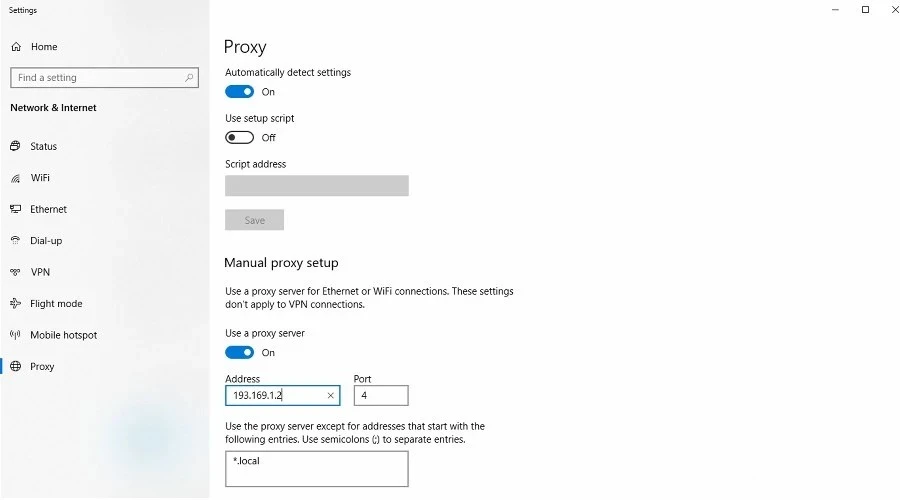
There are no such problems with proxies since they don’t encrypt. Your speed won’t be affected at all, but your IP address will be hidden, and you’ll get access to all the online content you wish.
You can even connect your proxy to your torrent client, and mask that as well. Many torrent clients have their own encryption system, too.
It’s not as powerful as the one used by VPNs, but it’ll do the trick.
Now, proxies mostly don’t come as an app, like VPNs, but instead, they’re more like add-ons for your browser.
There are many different ones, and here too you have the option to pay for one or to use the free one.
They’ll both give you access, but the free one is, again, not the best choice.
Mostly because it’s free, and everyone wants to use it.
That creates very bad traffic, so a bad and slow connection. Plus, you may get a lot of ads and there’s always the risk of tracking and data selling.
There’s also an option for proxy websites.
After you go to one of the proxy websites, you then use it to type in the address of the website that you wish to visit.
The proxy website will redirect you to the website of your choice but will act as a protection layer.
Basically, the site or service will see that someone’s visiting via proxy, but it won’t be able to determine who it is.
4. Other options
Proxies and VPNs aren’t the only way to hide IP addresses but are the most popular ones.
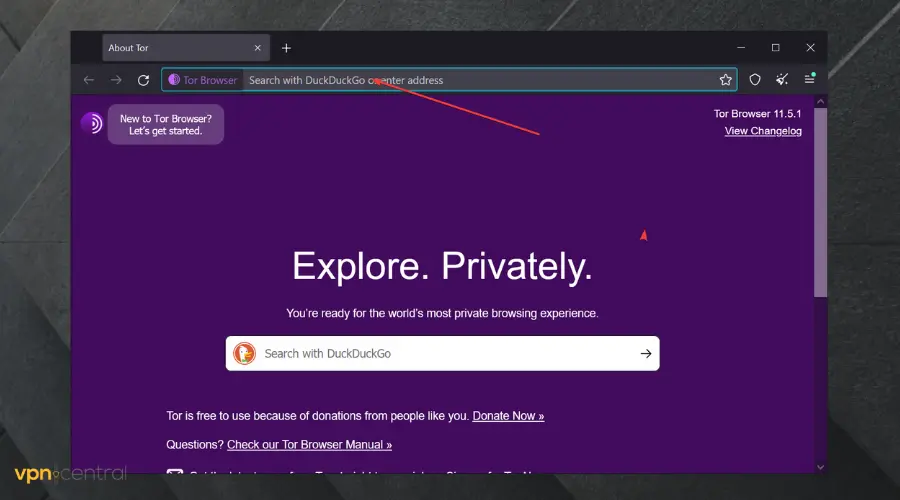
There are still some other options, like using someone else’s network to do your business or relying on anonymous browsers like Tor.
Your IP doesn’t travel with your device (laptop, smartphone, even desktop), but instead, it is tied to the router that’s giving you an internet connection.
If you decide to use a coffee shop’s or hotel’s connection, or any other sort of public internet, you’ll work on their IP, and then there’s no way of telling who you are.
All that potential trackers would know is that you’ve used one of the public connections, and that’s it.
It’s a high-quality service, and it basically works by sending your data around the world via a free, volunteer network.
Your data travels from one relay to another, until every connection to you is lost, and can’t be tracked back.
This has proven to be a very useful and successful way of masking your IP and content, but the downside is that it slows you down, a lot.
This is why Tor can’t be used for streaming or downloading, the process is simply too difficult for videos or downloads.
Still, it’s a decent alternative for regular browsing, and it’s also the only way for people to access the dark web.
You don’t have to be a hacker to use it, and many people do so, simply for protection and privacy.
Read more:
Conclusion
The Internet has become more than just a tool for work or killing time. It has become our window to the outside world, and many of us would feel incomplete without access to it.
Still, using it has its dangers, as we’ve discussed in this text, and it should go without saying that you need to protect yourself.
It could be a wonderful place full of possibilities if you use it right, or it could ruin your life if you don’t watch out. Information is the key, and you now have enough to decently protect yourself against the usual threats.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
1 messages